InfoSec Write-ups – Medium–
Hello Guys ! I am Jeya Seelan a Security Researcher and a Bug Hunter. This Is My First Bug Bounty Writeup. We are Going to See A Short Story of IDOR and How Could I Have Taken Over Your Account Through It.
Before Getting into Details Let’s See What is An IDOR.
What is an IDOR?
IDOR Stands For Insecure Direct Object Reference and it is a type Of Access Control Vulnerability. According to OWASP IDOR occurs..
“ Insecure Direct Object Reference occurs when an application provides direct access to objects based on user-supplied input. As a result of this vulnerability attackers can bypass authorization and access resources in the system directly, for example database records or files. Insecure Direct Object References allow attackers to bypass authorization and access resources directly by modifying the value of a parameter used to directly point to an object. Such resources can be database entries belonging to other users, files in the system, and more.”
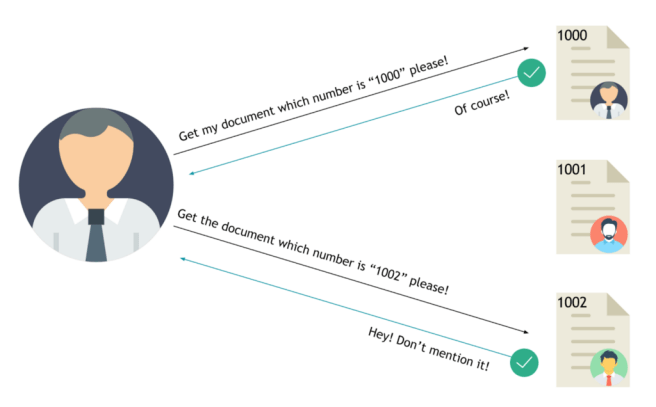
Let us See an Example, Consider Two Users User A and User B. The User-A is having a Document with ID 1000 and the User B is Having a Document with ID 1002.
In Normal Scenario the User A Will Only Have Access Only To Document With ID 1000 and User B Will Only Have Access to Document with ID 1002. But Here If User A Changed the Document ID to User B’s ID -1002, User A can Able to Access the Document of User B. This Is due to Broken Access Control And Insecure Direct Object Reference.
How I was Able to Takeover Victims Account
Let us Consider the Website As REDACTED.COM . I have Started My Hunting on The Website and Started Testing for Bugs Such as XSS And Other Bugs But I had No Success as The Input was Sanitised and Handled Properly. After Sometimes I Checked The Profile Update Page and Found an API Endpoint POST /updateprofiledata
The Body of The Request Contains A JSON Request With ID Parameter with Value of Users ID Number. So I decided to Play With The Request Using Repeater and I Changed the Value to Victims ID Boom the Response was 200 OK And the Details Got Updated On the Victims Account. But Still There Is No Severe Impact As We can Only able to Change Details Such As Name and Address Details.

After Sometime I thought Of Increasing the Impact of The IDOR. So I Decided to Look For Other Endpoints But there is No Luck for me. So I Played With the Same Endpoint and Added A email Parameter with Attackers Email in the JSON Request Boom my Request Got Successful and the Email is Changed to Attackers Email. Now I went To the Password Reset Page to Reset the Users Password. Finally, I have taken over The Victims Account Due to The Presence of IDOR.
https://medium.com/media/274fb5902cdb4278dff325a844969f2c/href
Thank you for Reading. If you enjoyed reading my article do clap and follow on Social Media handles :-).
Linkedin: https://www.linkedin.com/in/jeyaseelans
Twitter : https://twitter.com/jeyaseelans86
Medium : https://medium.com/@jeyaseelans
A Short Story of IDOR To Account Takeover was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
