InfoSec Write-ups – Medium–
Note: The primary aim of this article is not to pinpoint any individual SCAM, but to shed light on the methods adopted by Scammers/Attackers which peddles the Scam Business. Here, a Real-Life Use Case of SCAM is selected to provide detailed insight!
SS7 (Signalling System #7) is an interesting field where newbies often gets attracted due to its complexity and the recent architectural flaws. This interest is being monetized by Scammers.
A lot of traction has been gained on the design flaws of SS7 Architecture where Text/MM Messages, Calls, Billing and other services that are serviced on the cellular network (which are relied on SS7) are possible to be intercepted. The most popular Attack Vector in SS7 is the 2FA Bypass/Redirection which paves way for an attacker to directly access the control over victims phone remotely and can authorize any fraudulent actions performed by the attacker. This also results in siphoning out the money from Victim’s bank accounts.
Though the research had shown that: in order to carry out SS7 Attacks, there are various Work-Arounds such as setting up a fake tower (for large-scale campaigns), SIM Cloning (Individual) in order to intercept the messages/services successfully.
In short, if you come across a Hacking Service that offers SS7 Interception, probably it would be a Rat-Trap! Of-course, there would be legit services, but interestingly more scams gets popped-up/advertised on a large scale to the public via various mediums like Youtube, Instagram, Telegram, Public Forums and ultimately Dark Web.

Here, we are going to uncover such a new SCAM that is looming over the Social Media, which kick-started a couple of months ago.
SS7 is a Telecommunication standard that came into existence in 1984 by ITU Telecommunication. Various Cellphone services like Calls, Exchange of Messages, Number Portability and other innumerable cellular services are being operated under this protocol.
As a part of regular Dark Web Analysis, I just came across this site titled “SS7 Exploiter”, where various cellular exploitation services are being offered.
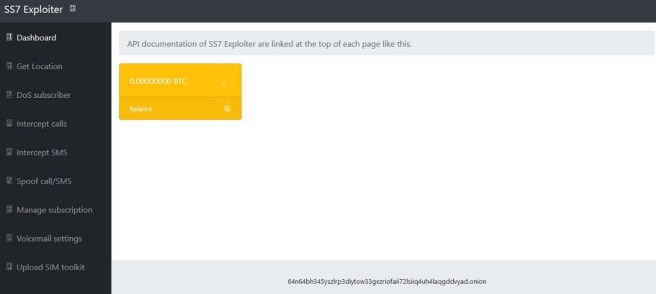
The design and the services listed itself is very alluring as it grabs anyone’s attention to try out the services. In order to use the services, the visitors are required to pay a sum of 0.005 in Bitcoin ($58 — ATTOW).
Here, I decided to tail this Dark Web Service as a sense of Scam is being felt. Upon a few searches, it is found that the same service is being advertised over Youtube and Instagram.
Following we are going to closely inspect Youtube Channel for Red Flags.
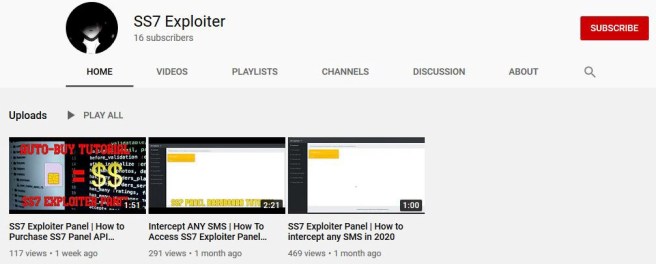
The actor had uploaded 3 videos in the time-span of 1 month. The channel got started on July 23, 2020; which overall gained 800+ Views, but this campaign started in the month of May.
In the videos, the actor had shown to install TOR Browser and open the SS7 Exploiter Dashboard Onion Website. The actor advises its viewers to make the payment in Bitcoin and the following price range had been shown:-
$50 for 1 Month Access
$80 for 2 Month Access
$120 for 3 Month Access
$350 for Lifetime Access
It is notable that the video does not show the demo of any listed services such as Call/Message Interception or Spoofing. Here is our first Red Flag detected!
By visiting the Onion site, it is notable that the system prompts the visitor to pay a sum of 0.005 to access the panel.
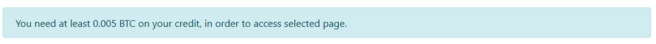
It is a psychological fact that people would be ready to pay a lesser amount before subscribing to the real product. But, what if a large number of non-tech savvy people come in contact with such banners! Yeah, that’s the real business!!!
In order to make the general viewers, the actor had made various swanking efforts by posting comments like :-
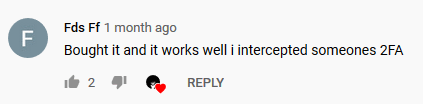
Here is our 2nd Red Flag detected!
Any serious questions posted under the comment section of listed videos are advised to contact directly over DM (Direct Message) on the actor’s Instagram Page. Again, a smart way to evade the attention of the public. Over the DM, the actor may be conducting extortion campaigns by presenting fake screenshots/programs to the potential customer, hence reaping maximum profits.
During Comment Scooping, another interesting fact uncovered. A comment is being spotted in Portuguese (apart from English).
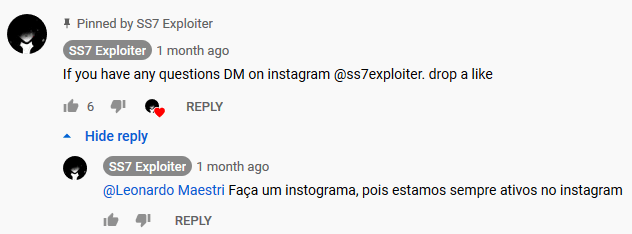
The comment translates to:- “Make an instogram, as we are always active on instagram”.
From this, it can be assumed that the account holder is either from Brazil or Portugal where the local language of the actor is set to Portuguese.
MODUS OPERANDI IN YOUTUBE
>>The attacker supplies the Onion URL directly: 64n64bh345yszlrp3diytow33gxzriofaii72lsiiq4uh4laqgddvyad.onion
>>The same URL is shared as a Text file which is hosted in SendSpace (a File Sharing Site).
>>Insists the users to pay in Bitcoin to access the SS7 Dashboard.
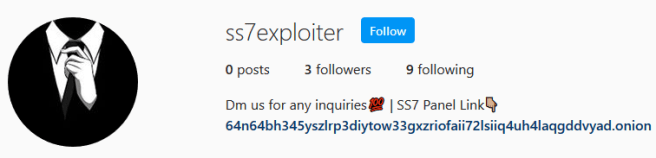
>>Asks the visitors to follow actor’s page on Instagram with the handle “ss7exploiter”.
>>Used various tags like #ss7 #ss7dashboard #ss7panel to get better search result for like-minded audiences.
Here is the Instagram handle of the actor
After detecting 2 Red Flags, I headed towards the Onion Site for further inspection. There found another evidence:-
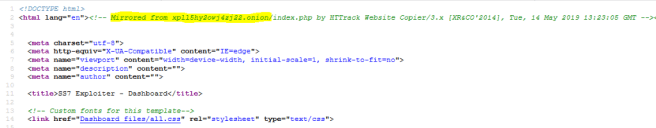
Upon checking the source code of the same, it is found that the SS7 Exploiter Dashboard is being mirrored (copied) using popular software HTTRACK (Open-Source Website Copier) from another Onion Domain xpll5hy2owj4zj22.onion which was active in the September, 2019 (not active anymore ATTOW). It can be assumed that the expired onion service might also be a scam page like SS7 Exploiter.
3rd Red Flag Detected!
Note: Copying or Mirroring a service is not illegal/unfamiliar with permission, but as we have detected 2 Red Flags earlier, we can classify it under fraudulent activities!
Now let’s explore the Monetization of SS7 Exploiter Service!
By checking the Bitcoin Address 18tBoUZtCK8BVWzRe3tQeaxbiQe5pjcPRs it is found that the scammer had made ~$2,100 in 3 months!
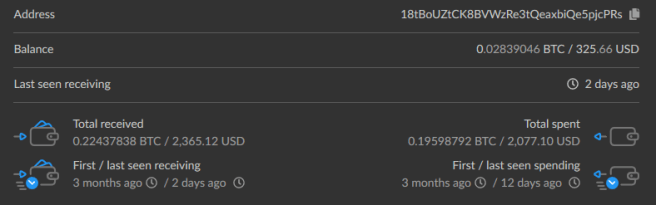
In order to track the initial transaction hit the scammer’s wallet, I delved deep into the address to track the date and following information is retrieved:-
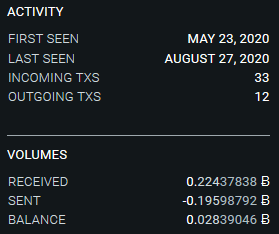
This indicates that the actor might have set-up the site in the month of May, 2020.
On further analysis, it is found that IPs 35.208.254.89 and 136.56.170.96 that are assigned to Google IPs that are relayed by Bitnode.
“Bitnodes is currently being developed to estimate the size of the Bitcoin network by finding all the reachable nodes in the network. The current methodology involves sending getaddr messages recursively to find all the reachable nodes in the network, starting from a set of seed nodes. Bitnodes uses Bitcoin protocol version 70001 (i.e. >= /Satoshi:0.8.x/)”
Another interesting fact found here is: All the Bitnode are running on the Port #8333, which is dedicatedly used to run a Full Node (of Bitcoin).
By delving deep into the Bitcoin Transaction Trails, following information can be extrapolated:-
35wu2BtEmcVTKV5g6za7XeZnGxcX3FEkEn : $1 — Aug 18
3CSeY9MFcug7DV3GQxL3tBEz9oTVRuAKzm : $40
3NFGErTqALRz5VwduTktEa6VSv8m1A6n23 : 200$ — Aug 16,2020
3F8rFNH4Yoz7Cc6LdA92kryZ4rFGBDSYSi : $8 — Aug 16,2020
3C2fztnpPMsJq8Pi8PeQYcidsyiA8FKx4s : $200 — Aug 11, 2020
3DeS9Ve85ZMxLsvKBn4rmJU1NuT5bd5TXK : $9 — Aug 8,2020
3G6BHZGJD7YyxKc3PqU6Wu9Jp8RoxYoT87 : $31 — Aug 2, 2020
3N5p2xSQq6GGYWLTeo6CpSCw3fCMgVXatx : $312 — Aug 1,2020 3KoKHJmJ1PrgjNRcp7MUY2sERUdjRfYvUp : $298 — July 31st
3M9BXsco3jSourpYUeMNTCeJft5HWNHGkU : $19 — July15
1JKYwjEDQ4MYe2Hrsk2ZzWncKRaiSWDLQb : $386 — June 20
3M7zFT3KzLZkpKjiJJBPEvQbN8fSidYdaj : $410 — June 10
These are the transactions initiated by the actor from the publicly facing Bitcoin Address (which is listed on SS7 Exploiter Panel) to the actor’s personal account.
Note: It is a rule of thumb in the Crypto Community to transfer the fund to any other Wallet Address in order to segregate the funds from public facing Wallet Address.
On further analysis, it is found that the initial address 3M7zFT3KzLZkpKjiJJBPEvQbN8fSidYdaj is mapped to a Coinbase account where the scammer had transferred $410. Another important fact to highlight is 3CSeY9MFcug7DV3GQxL3tBEz9oTVRuAKzm would be probably a Bitcoin Mining Farm, where the scammer had invested a sum of $40.
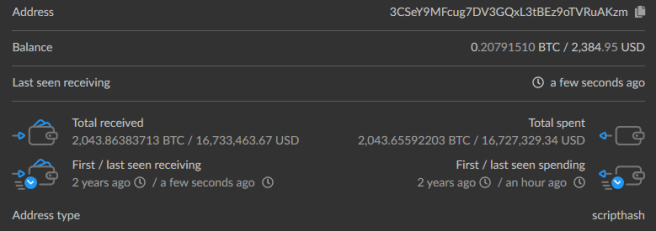
So, the Scammer/actor had also invested a tiny amount in Bitcoin Mining in order to reap maximum profit.
From the efforts listed above, it is clear that the Scammer is trying to reap maximum profit by advertising the platform on various Social Media Channels for larger audience coverage. It is also evident that the scammer is targeting people who are less Tech-Nerds and mostly teenagers and would continue to increase the SCAM Activity over the course of time.
KEY TAKEAWAYS
>>Not to trust any hacking services without conducting background checks
>>Never pay anything even if the demanding amount is minuscule
>>Do not fall for the fake generated reviews/comments
>>Try to learn the underpinning technology, rather than looking for a silver bullet in InfoSec
>>Regularly communicate your thoughts to the InfoSec Community
Note:- The Article is purely an Individual Research and is not subjected to be used/published anywhere without the Author’s consent.
Follow me on Twitter for interesting DarkWeb/InfoSec Short findings! 😉
SS7 Attack Panel: Yet Another Rising SCAM on Social Media was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
