InfoSec Write-ups – Medium–
WebGoat SSRF 2
After watching this mind-blowing talk about SSRF from Orange Tsai
https://medium.com/media/9d02af942d527d802d6ffec391efd2c0/href
let’s see what’s in this lesson
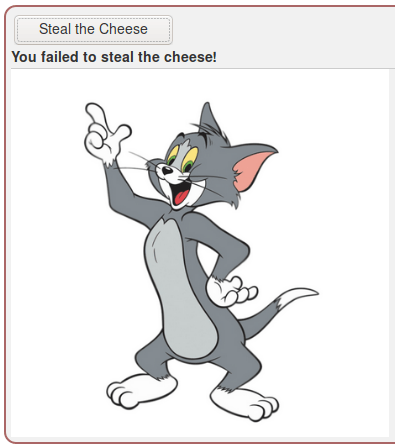
Press the button and we get Tom
The lesson explicitly tells us to change the URL to “jerry”
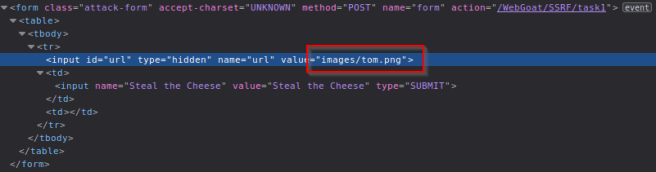
Inspect the button with your browser dev tool, find the hidden input and change the URL from “tom” to “jerry”
Press the button again and the lesson is completed
WebGoat SSRF 3
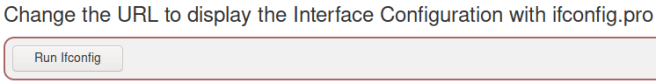
Press the button
To stick to the game plan we could check if there is something like the last lesson in here

Change the hidden text input to “http://ipconfig.pro" thus asking the server to request the page
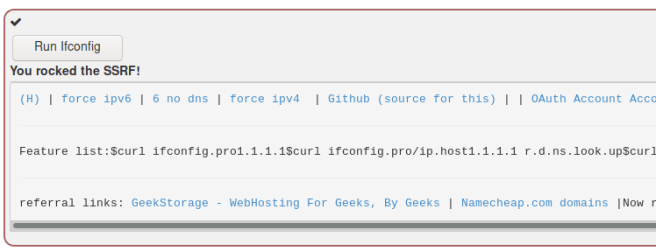
Press the button again and the lesson is completed
And remember to go check http://ipconfig.pro/ to check its functionalities
This concludes WebGoat SSRF 2 3
I hope you liked it.
PVXs — https://twitter.com/pivixih
WebGoat SSRF 2 3 was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
