InfoSec Write-ups – Medium–
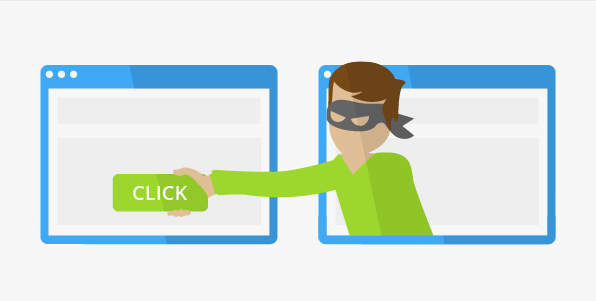
Hello everyone today I am going to tell you how I did from Clickjacking to full account takeover so if anyone doesn’t know what is Clickjacking then I tell you in brief.
Clickjacking is the attack that tricks a user into clicking a Webpage element which is invisible or disguised as another element. This can cause users to unwittingly download malware, visit malicious web pages, provide credentials or sensitive information, transfer money, or purchase products online.
Typically, Clickjacking is performed by displaying an invisible page or HTML element, inside an iframe, on top of the page the user sees. The user believes they are clicking the visible page but in fact they are clicking an invisible element in the additional page transposed on top of it.
The invisible page could be a malicious page, or a legitimate page the user did not intend to visit — for example, a page on the user’s banking site that authorizes the transfer of money.
So I can’t disclose website name let’s take it as target.com I found Clickjacking vulnerability in the website.
To test Clickjacking vulnerability you can use this online tool
Clickjacking Tool | Test | UI Redressing
And also You can use this html code
<html>
<head>
<title>Clickjack test page</title>
</head>
<body>
<p>Website is vulnerable to Clickjacking!</p>
</body>
</html>
I found vulnerability but then I have to show the impact so when I logined to the website I saw that we can easily change the email address as there is lack of password confirmation so I made a POC and reported to the website. I didn’t get bounty as they don’t have their bug bounty program but I got hall of fame on their website.
Tip:if you get Clickjacking vulnerability then show the impact like deleting the account, changing email address, disabling 2 FA.
The mitigation from Clickjacking attack is to Use X frame options and Content Security Policy you can read about them from below link:
Thank you everyone and have a nice day.
How I Did Full Account Takeover By Clickjacking was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
