InfoSec Write-ups – Medium–
Note:- This is an investigation which kick-started by targeting a Crypto Platform and gradually uncovered a series of other fraudulent services
As a part of my daily TOR surfing, I stumbled upon a post in Dread titled “Cryptobay.cz”. By the title, I figured out that it is a new Crypto-Laundering Services like Tumbler or Mixer out in the market.
But wait…It’s just the reverse — Trade Clean Bitcoins for Dirty (stolen) ones!!!
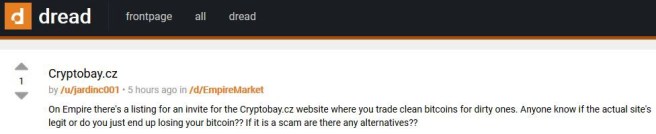
The OP’s question hinted that s(he) is interested to purchase dirty bitcoins with clean bitcoins (risk included!), regarding whether the service is genuine or not had intrigued me to tail the same.
As visiting, the site seems legit with a few vendor profiles and other listed offers (some are tagged as “SOLD OUT” in order to solidify trust of the newcomers -who knows…)

A bunch of various vendor profiles had been spotted, with certain BITCOIN requesting for “clean” money; in order to evade detection as these are either stolen (quoted as “dirty”) or acquired via other criminal dealings.
Here is an example for a vendor profile handle “Warrica” who is from Russia and claims to have stolen 27BTC (about $1,93,266) from Binance Exchange.
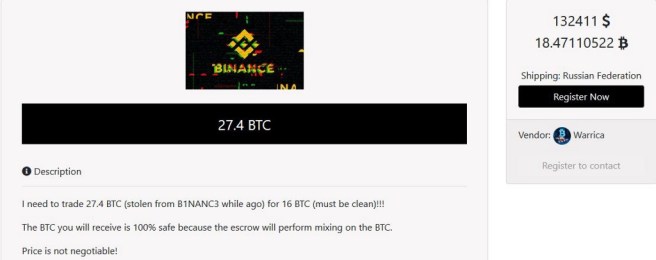
Since there are few vendor profiles with high rating; we can’t conclude whether the service is legit or not, as there is no substantial evidence to back it up (feedback pages are empty).
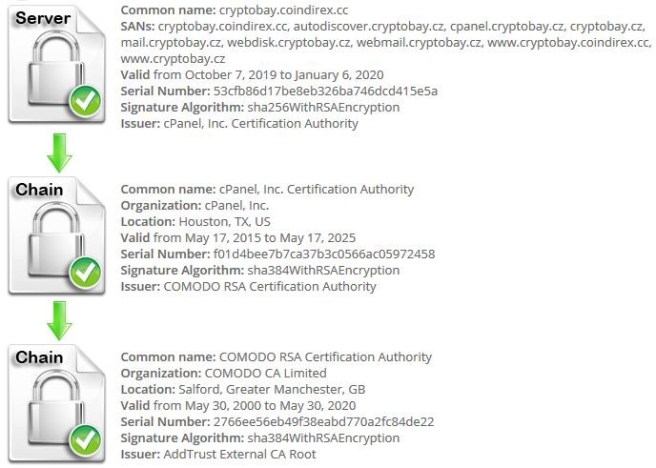
On analyzing the certificate and other comments, it is found that the site is directly associated with CoinDirex; which is a Digital Asset Exchange based in Ghana.
However, CryptoBay had done a handful of right things in order to lure the new customers to seal their trust such as:-
- SSL Certificate (which is Legit)
By analyzing the SSL Certificate, the following things are found:-
cryptobay.cz resolves to 78.142.19.148
Server Type: Apache
The certificate should be trusted by all major web browsers (all the correct intermediate certificates are installed).
The certificate was issued by Sectigo.
The certificate will expire on January 06, 2020
The hostname (cryptobay.cz) is correctly listed in the certificate.
2. Bogus Customer Review
Although many vendor profiles are rated positively, when navigating to the feedback page, most of the pages are left blank.
3. Protected by imunify360
As the SSL is verified by cPanel, it is found that there is an add-on offered by cPanel named “imunify360” is being installed as an add-on along with the approval of SSL Certificate from cPanel.
4. Interactive Website Design
To gain trust, as the visually perfect things are more appealing to the human mind, to move further with the hope to do business.
During the deep-down analysis, it is found that: Most of the vendor profiles found on CryptoBay.cz are banned/suspended on CoinDirex.
[So it can be assumed that the banned vendors might have used their past credentials(from CoinDirex) in order to get a new SSL certificate for CryptoBay….or something else?]
Let’s drill down…
Alleged IP Address: 78.142.19.148
===================
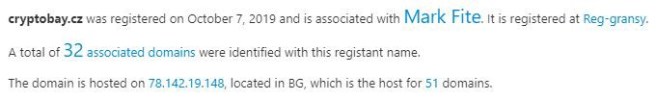
On a plain lookup, it is found that the site is hosted in Bulgaria by Beehosted-BeeBox-LTD
On further lookup, the following things are found:-
domain: cryptobay.cz
registrant: SUB-1148892
admin-c: SUB-1148892
nsset: SUB-20191007152007
registrar: REG-GRANSY
registered: 07.10.2019 15:20:07
changed: 16.11.2019 02:13:04
expire: 07.10.2020
contact: SUB-1148892
name: Mark Fite
address: 1670 Upton Avenue
address: Limtestone
address: 04750
address: ME
address: US
registrar: REG-GRANSY
created: 07.10.2019 15:20:06
nsset: SUB-20191007152007
nserver: lunar1.freednsdedi.com
nserver: lunar2.freednsdedi.com
tech-c: SUB-1148892
registrar: REG-GRANSY
created: 07.10.2019 15:20:07
78.142.19.148 — Large Compilation of Fraudulent Services Hosted
As CryptoBay is pointed towards this IP Address, it is found that there are other websites hosted on the same IP Address- which are malicious!!!
51 Domains, 327 Sub-Domains and 477 Name-servers are found the same IP Address in which most of them are malicious.
Here is the list of Domains:-
avastcustomer-service.com
citicapitalbank.com
contactbelgie.com
desixnxx.pro
dpexpress.co.uk
eutanasiacondignita.com
fastspeed.host
golderson.com
gr8iptv.net
homzsecpl.com
kuncha4u.com
medizinischernembutal.com
microsigln.com
offerslash.com
onlinercshop.com
qualitymedsonline.com
rxbestchoice.com
seriesyonkis.org
signlogs.com
unusedcodegenerator.com
wefappy.com
wp-nulled.com
gplayprizes.com
xboxlivezone.com
jstash-bazar.org
seriesly.org
jstash-bazar.net
jstash-bazzar.com
uniccbazar.com
unicc-bazar.net
uniccbazar.net
unicc-bazar.biz
attsupportdesk.com
facebook-visitors-canada.com
facebook-visitors-ca.com
fbtimelinestalkers.com
fbtimelineviews.com
patente-compra.net
cryptonomize.net
videos-porno.net
After going through the above list, it is notable that there are many phishing sites of popular services such as Avast, AT&T, Microsign, Fast are hosted.
Rest of them are the fake CVV Shops (of real CVV sites) with the similarly-spelt domains such as Jstash-bazar.net (which is fake for “jstash.bazar” which is a genuine blockchain site).
Here are some of the sites (scan report included) that are reported malicious:-

Others associated with Mark Fite are:-
mfite@optiontechnologies.com
nocontactsfound@secureserver.net
farkmite@gmail.com
Option Technologies Interactive LLC
Attn Optiontechnologies.net
Attn Audienceresponsetools.com
(We won’t focus on Actor Profiling, as the research is centred around the malicious services hosted on single IP Address)
This again indicates that CryptoBay.cz holds all these Red Flags (to avoid, in case if anyone wonders), as it is one of the domains hosted in the same malicious network.
Key-Intakes
From the above case study, the following things can be observed:-
Blacklist the IP Address — if it is associated with more than 2 malicious services.
Banned/Excommunicated members could come together and can kick-off another malicious campaign, which can form as an Organized Digital Crime.
Every genuine service (including offensive) provides support on either Reddit, Dread or any other social media platform. If that’s missing, skip it.
Phishing Sites of popular sites are optimized with simple keywords to obtain high page ranks in order to pop up at the initial search. Always go to the legitimate sites (avoid links from email/blogs) for any queries.
Keep an eye on the Hosting Provider — who is having the previous track records for hosting malicious websites — in this case : Beehosted-BeeBox-LTD
Note:- The article is purely an Individual Research and is not subjected to be used/published anywhere without the Author’s consent.
Follow me on Twitter for interesting short InfoSec/DarkWeb Discoveries! 😉
CryptoBay.cz Analysis: A Bunch of other Fraudulent Services hosted on a Single IP Address Revealed was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
