InfoSec Write-ups – Medium–
Let’s secure WFH in Kerberos way!
People are mostly quarantined which poses a major challenge to work securely for the company as well as for employees. Both parties are worried about a single topic of “Security”. Companies nowadays are working to make secure login for seaming experience, also employees are looking for 1-click access feature. Let’s see how the big MNC solves the problem.
Imagine, you are WFH and want to connect to a remote application over an insecure network (TCP/IP), also parallelly in some space …
*Le Hackers: “Here is the data feast coming, gear up company! Hehe …”
So now you are worried that someone might breach in, someone might get access to your messages or someone might impersonate you at places?
Hmmm…So now you need a “rule” which is designed to provide secure authentication to services over an unsecure network.
Additionally, on a broader domain :
- Credentials should never be shared across networks.
- Encryption keys for either side should be never directly exchanged.
- Mutually both client and server should authenticate each other.
- Clients are able to perform SSO(Single Sign-On) into applications.
A protocol that can do all of the fore-mentioned steps is “Kerberos”.
Let’s dig deep into various aspects,
- What is Kerberos Protocol?
- Mythology Behind The Name
- Terminology
- Step by step guide
- Fun Facts using QnA
- Other Important Insights
Without further ado, let’s start!
What is Kerberos Protocol?
Kerberos is a computer network authentication protocol that is been implemented in a client-server architecture. In simple words, the Kerberos protocol will build a secure communication link between two trusted hosts across an untrusted network like the Internet using tickets. (How? We’ll see below :p)
it will authenticate two hosts using the shared secret authentication technique. It will share a secret among the two hosts that only them and KDC know. To understand the shared secret technique (symmetric key), if two people share a secret code that only they know they can use that to authenticate themselves. This is called symmetric key encryption because both parties share the same key which can use to open any message or data that pass between them.
In more technical words this single key must be capable of both encryption and decryption.
Basically, Kerberos comes down to just this:
- A protocol for authentication
- Uses tickets to authenticate
- Avoids storing passwords locally or sending them over the internet
- Involves a trusted 3rd-party
- Built on symmetric-key cryptography

Mythology Behind The Name :
Kerberos’ name from the Greek word “Cerberus”. perhaps means “Death-Daemon of the Dark” comes from the 3 headed dog. It’s If anyone interested in trivia, Cerberus is the three-headed guard dog at the gates of Hades who is the god of the underworld according to Greek mythology. It’s a fitting name for this system as it uses a trusted 3rd party name KDC (Key Distribution Center) to authenticate between a server and a client.

Terminology
- Kerberos Realm — It is the domain the group of systems over which Kerberos has the authority to authenticate a user to a service.
- Principal — A principal is a unique identity either a user or a service an application. Within a realm you have principles.
- Client/Users — A client is a process that accesses a service on behalf of a user. Usually, we exchange the terminology and that’s okay. There can be multiple users within a realm.
- Service — It is a resource provided to a client, for example, a file server or an application that a user wants to access for eg: file server. Definitely, one can have multiple services the client can access.
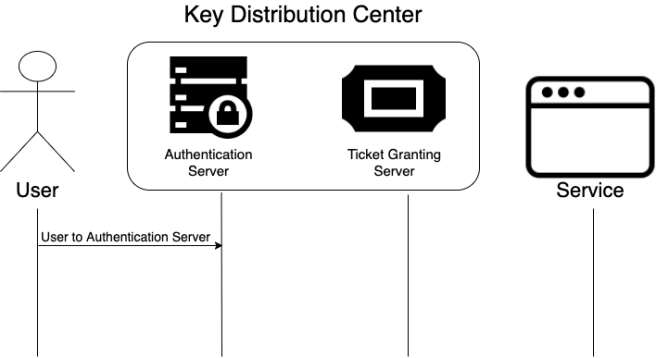
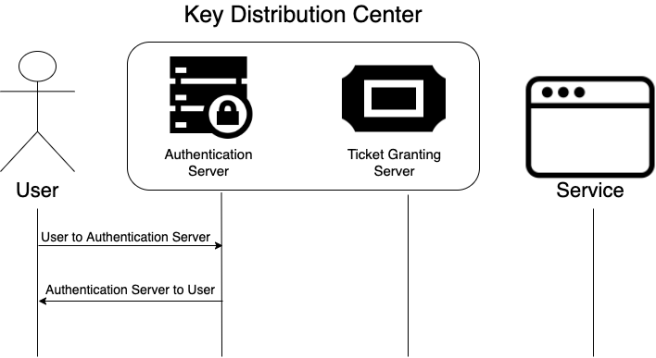
- KDC(Key Distribution Center) — It is the heart of Kerberos that supplies tickets and generates temporary session keys that allow a user to securely authenticate to a service.
It has 2 servers within KDC to carry out process: Ticket Granting Server and Authentication Server. - Ticket Granting Server (TGS): The server confirms that a user is making an access request to a known service and issues service tickets.
- Authentication Server (AS): This server validates that a known user is making an access request to services and issues ticket-granting tickets.
- Authenticators — These allow the user to authenticate to the service and the service to authenticate to the user mutual authentication.
- Tickets — This contains most of the information that needs to be passed the clients' identity service ID, session keys, time stamps time to live etc all encrypted using a servers secret key.
Hmm…! That’s a lot. jargon words.
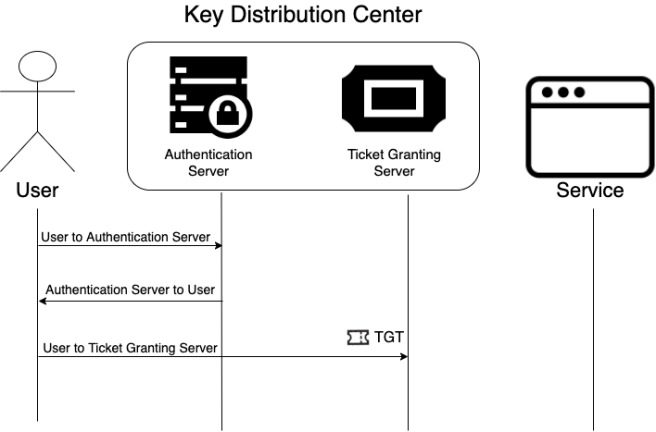
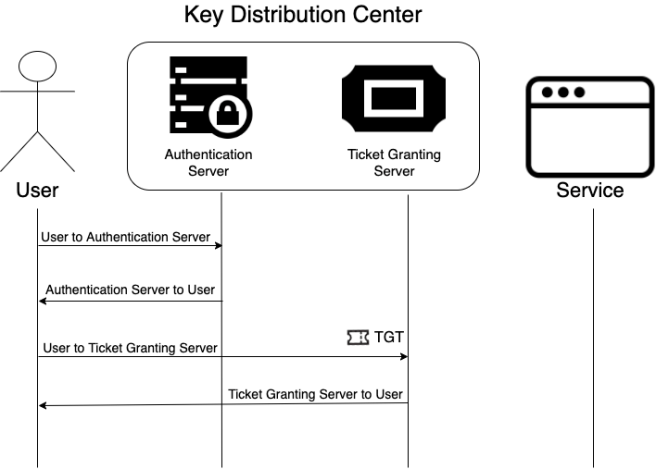
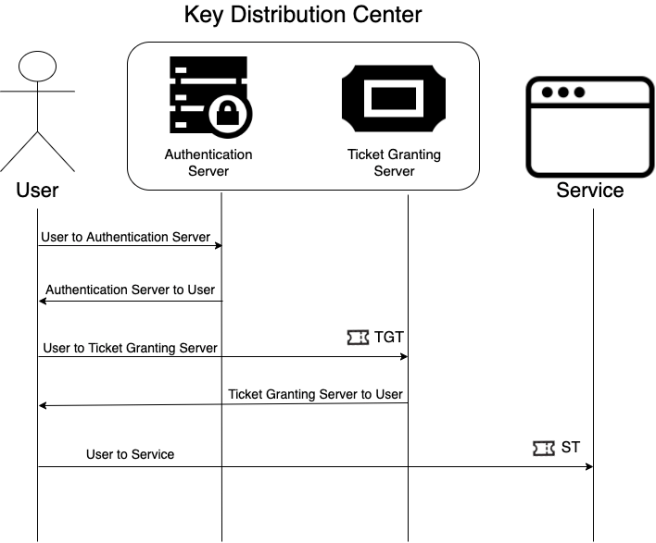
Step By Step Guide
Let’s look at a high-level overview of the communications that occur for a user to gain access to a service.
Step 1: We start with the user sending an unencrypted message to the authentication server saying, “Hey I’d like to access some service”.
Step 2: The authentication service validates the request is coming from a known user and generates a Ticket Granting Ticket. The TGT is sent back to the user along with another message encrypted with the users secret key.
Step 3: The user decrypts the message with their secret key and then it creates a couple of new messages and sends the new messages along with the TGT on to the ticket-granting service.
Step 4: The ticket-granting service decrypts the ticket-granting ticket performs some validation and generates a service ticket the service ticket along with another message is sent back to the user.
Step 5: The user decrypts the message creates an Authenticator message and sends the user Authenticator and the service ticket to the service.
Step 6: The service does its own decryption validation and creates its own final Authenticator message. This final Authenticator message is sent back to the user.
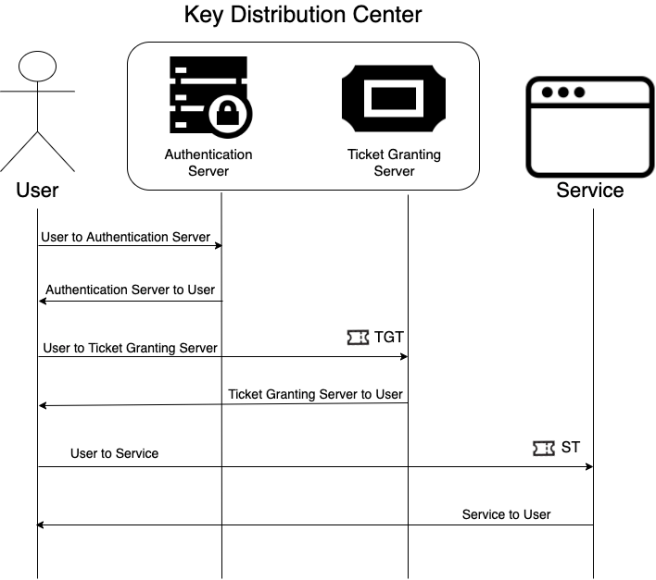
All of these messages allow the user and the server to mutually authenticate each other and securely distribute asymmetric service session key which allows the user and the service to communicate authentication information securely.
Fun facts using QnA!
- Who actually invented Kerberos and when? Kerberos is a stateless network protocol developed by MIT and considered as licensed for distribution and modification. Kerberos started as part of Athina (another mythology reference!) project in 1979, aimed at protecting MIT computer networks.
- What makes Kerberos so special? Kerberos uses secret-key cryptography to provide secure communication over non-secure channels. Essentially, Kerberos is a trusted 3rd party server that issues tickets for users so they can authenticate to systems and services.
- Which Kerberos feature made it so valuable for organizations? Although it may seem strange and perhaps somewhat naive, it became valuable because the implementation for Microsoft and Mac devices used DES encryption.
- What is a Kerberos ticket, in a nutshell? Kerberos uses tickets to authenticate and grant access. Tickets created by a ticket-granting server (TGS) are trusted by the authentication server, to a specific service or endpoint requested by an account. Ticket serves as a proof of (your) identity and is always encrypted with a secret key. As long as your Kerberos ticket is valid, you will get access to the system or service.
- How is exactly client-server architecture followed? In Client-server architecture client will send a request to the server requesting the service and server will respond by providing service to the client. But before starting the process, the client should be authenticated bt the server, and vice versa.
- Is it a pure single-side client-server model or can it be used for mutual identity verification? Yes and yes. It is a mutual handshake where the client and server can verify each other’s identities. They accomplish this by using the encryption of timestamp with joint session key or via challenge/response that was introduced in 2005 to solve associated vulnerabilities.
- What is a “Pass the Ticket” attack? Attackers can use tools such as Mimikatz and Windows Credential Editor to mine Kerberos tickets from compromised user endpoints or from authorization servers. Once the hacker gets a hold of these tickets, they can laterally move around the network to see privileges and harvest information that can help them gain access to critical systems.
- What about ‘Golden Ticket’? This is called a ‘Golden Ticket’ because you are granted indefinite creation of a Kerberos generating ticket which is usually hardcoded to grant access for 10 years by default, but changeable.
- Are encryption keys kept unencrypted in memory during protocol use? Yes, that is a fact. Try not to think about this too much; this just makes the call execution faster.
- If Kerberos is supposed to be secure and widely trusted, do I still have to use strong passwords? Passwords are, unfortunately, here to stay as they are used to encrypt the certificates. Failing to use strong passwords will allow for a brute-force attack.
- How Single Sign-On (SSO) capability is boosted using Kerberos? When the user is authenticated for the first time, it stores the ticket service to the browser cache for TTL. This enables them to auto-authenticate to service.
Other Important Insights :
- The KDC stores all of the secret keys for user machines and services in its database.
- These secret keys are all stored in the KDC database.
- Kerberos can be interpreted as a system. It contains 3 parts. Authentication server to check the authenticity of the client by checking whether the client has a master key, Ticket Granting Service to grant tickets to authorized users and the database to store the client details (This is just like a small validation database).
- The KDC itself is encrypted with a master key to add a layer of difficulty from stealing keys from the database.
If you feel some insights miss, directly hop in the comments section and write your heart out. Open for edits, suggestions and comment. Press and hold the applaud if u think it deserves.
Have a Happy WFH 🙂

Let’s secure WFH in Kerberos way ! was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
