InfoSec Write-ups – Medium–
CVE-2020–24115
Use of hardcoded credentials in source code leads to admin panel access
# Exploit Title: Online Book Store 1.0 — Use of Hard-coded Credentials in source code leads to admin panel access
# Date: 2020–07–22
# Exploit Author: Mayur Parmar(th3cyb3rc0p)
# Vendor Homepage: https://projectworlds.in/free-projects/php-projects/online-book-store-project-in-php/
# Software Link: https://github.com/projectworlds32/online-book-store-project-in-php/archive/master.zip
# Version: 1.0
# Tested on Windows10
# CVE: CVE-2020-24115
Hardcoded Credentials:
Hardcoded Passwords, also often referred to as Embedded Credentials, are plain text passwords or other secrets in source code. Password hardcoding refers to the practice of embedding plain text (non-encrypted) passwords and other secrets (SSH Keys, DevOps secrets, etc.) into the source code. Default, hardcoded passwords may be used across many of the same devices, applications, systems, which helps simplify set up at scale, but at the same time, poses a considerable cybersecurity risk.
Attack Vector:
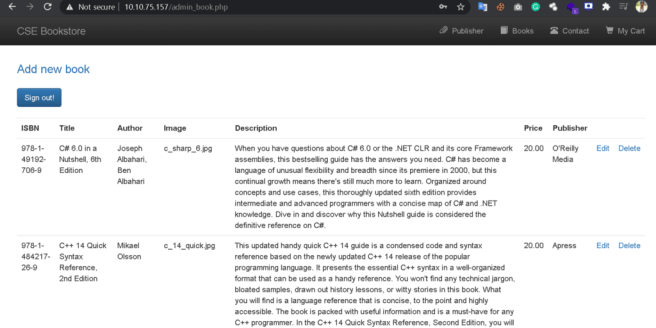
An attacker can gain admin panel access using default credentials and do malicious activities.
Steps to reproduce:
- Download source code from https://projectworlds.in/free-projects/php-projects/online-book-store-project-in-php/
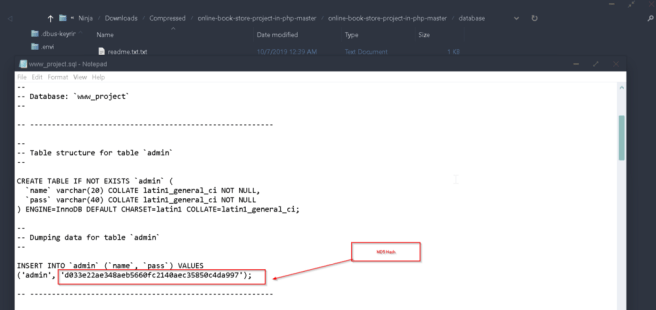
- Now unzip it and goto Database folder here we can see one SQL file.
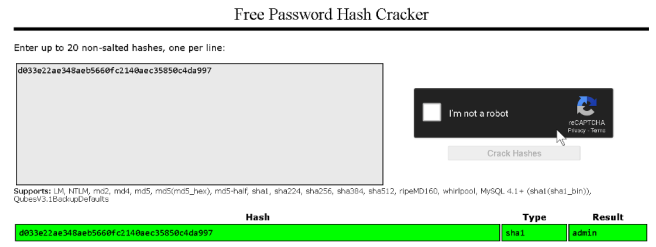
- Now open that file using Notepad and there we can see admin credentials. but the password is encrypted .from pattern I identified that this is MD5 hash. so we can easily decrypt using crackstation.net or any hash cracker tools like Hashcat, John the ripper.
4. Now we have Admin credentials so we can easily log in to the portal.
Mitigation:
- Always use a strong encryption algorithm like SHA-256 with SALT.
- Never use default credentials always change during installation time
CVE-2020–24115: Use of hardcoded credentials in source code leads to admin panel access was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
