InfoSec Write-ups – Medium–
TryHackMe: OWASP Top 10(Day 1) Beginner friendly walkthrough
Walkthrough [Day 1] Injection TryHackMe
Room Link: https://tryhackme.com/room/owasptop10
Recently TryHackMe released ten days OWASP Top10 challenges where beginners will learn OWASP top 10 practically.
Connect to the tryhackme network using OpenVPN using below link
Now goto owasp top 10 room using below link:
https://tryhackme.com/room/owasptop10

[Day 1] Injection
below I provided some resources to cover the theory part of the Injection attacks
https://owasp.org/www-project-top-ten/OWASP_Top_Ten_2017/Top_10-2017_A1-Injection
OWASP Top 10: Injection – DeepSource
[Day 1] OS Command Injection:
refer below link for OS command injection
Now we have given the practical.

Goto Task6 and click on the Deploy button. Make sure that you have connected to tryhackme network using OpenVPN.
after that, they assign the IP address of that machine. wait for 1 to 5 minutes because tryhackme servers take some time to deploy the machine.
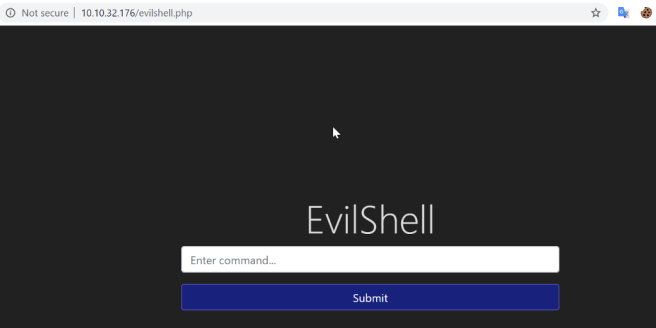
After that, you will get a webpage like this.
Refer below link for OS commands that are useful while doing pentesting
https://securityonline.info/some-useful-linux-command-for-your-penetration-testinglinux-command/
#1 What strange text file is in the website root directory?
- by typing pwd command I got the directory that is /var/www/html. from this I’m able to know that I’m in the root directory.
- Now I used ls command to list the files in the directory.
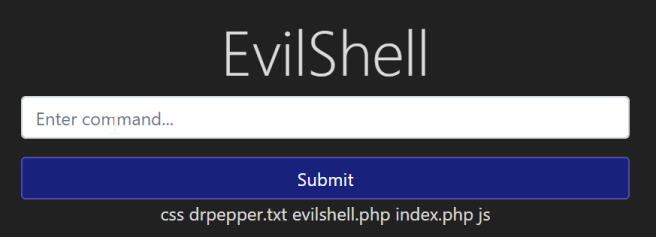
From the above screenshot, I got to know that drpepper.txt is a strange file.
Ans: drpepper.txt
#2 How many non-root/non-service/non-daemon users are there?
Ans: As I already know that this is a Linux machine. anAndinux store all the username from the passwd file that is located in the /etc/passwd directory.
so I quickly typed cat /etc/passwd command to show the content inside passwd file
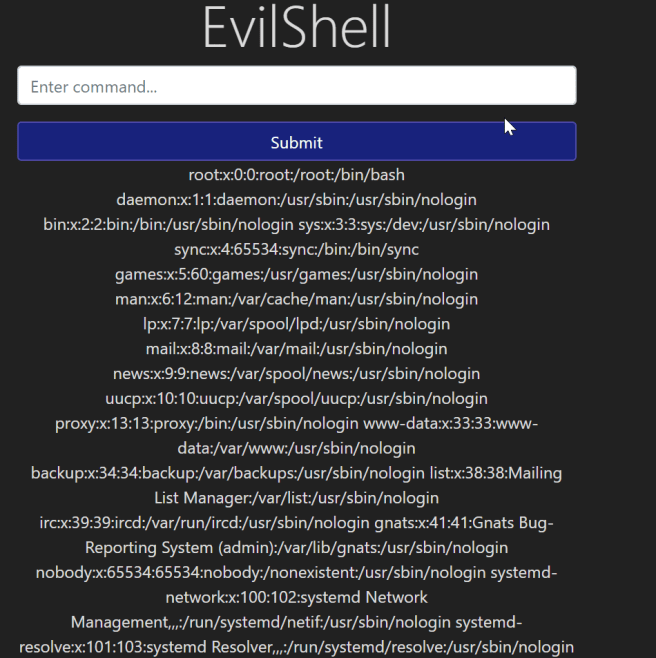
form this output I observed that there are no non-root/non-service/non-daemon users are present.
so our the answer is 0
#3 What user is this app running as?
Ans: This question is vestraightforwardweWean use whoami command to check that which user is running this application.

form the above output we can see that www-data user is running this application.
#4 What is the user’s shell set as?
Ans: As we retrieved the passwd file that contains all the user’s information. from that, we can retrieve that which permission is allowed to that user.
from below output, I highlighted the user part & we can see that user’s shell information.
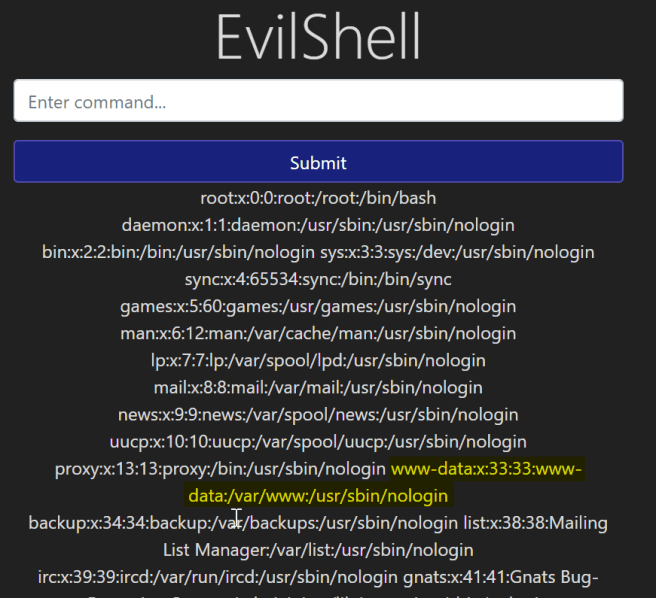
Answer: /usr/sbin/nologin
#5 What version of Ubuntu is running?
Ans: for this question, we can use Linux’s inbuilt command to know the version os the OS.
command: lsb_release -a

Reference:
https://www.cyberciti.biz/faq/how-to-check-os-version-in-linux-command-line/
Answer: 18.04.4
#6 Print out the MOTD. What favourite beverage is shown?
Ans: For theory part of what is MOTD follow below-given link.
at this time I’m not aware of this MOTD file. so I quickly googled about this file and got to know that this file is used to send a common message to all users in a more efficient manner than sending them all an e-mail message.
& this file reside in /etc/ directory. so quickly used locate command to find all the files that have motd name inside it. from the below result I figured out the correct file.
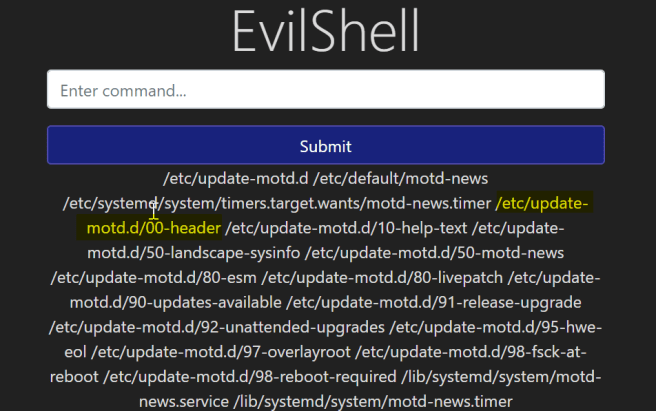
after that, I used cat command to show content inside file.
command: cat /etc/update-motd.d/00-header

as in the question they asked for beverage & from the output in the last line, I got the name that is DR PEPPER.
Note: Next part will be released tomorrow.
References:
https://securityonline.info/some-useful-linux-command-for-your-penetration-testinglinux-command/
Author: Mayur Parmar(th3cyb3rc0p)
https://twitter.com/th3cyb3rc0p?lang=en
https://in.linkedin.com/in/th3cyb3rc0p
https://www.instagram.com/th3cyb3rc0p/?hl=en
https://twitter.com/cyberdefecers?lang=en
TryHackMe:OWASP Top 10(Day 1) was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
