KitPloit – PenTest Tools!–
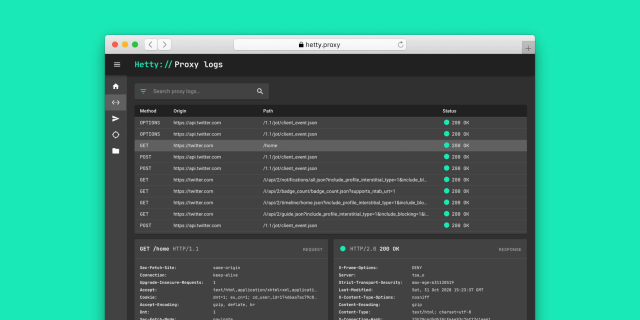
Hetty is an HTTP toolkit for security research. It aims to become an open source alternative to commercial software like Burp Suite Pro, with powerful features tailored to the needs of the infosec and bug bounty community.
Features
- Man-in-the-middle (MITM) HTTP/1.1 proxy with logs
- Project based database storage (SQLite)
- Scope support
- Headless management API using GraphQL
- Embedded web interface (Next.js)
v1.0 release. Please see the backlog for details. Installation
Hetty compiles to a self-contained binary, with an embedded SQLite database and web based admin interface.
Install pre-built release (recommended)
Downloads for Linux, macOS and Windows are available on the releases page.
Build from source
Prerequisites
Hetty depends on SQLite (via mattn/go-sqlite3) and needs cgo to compile. Additionally, the static resources for the admin interface (Next.js) need to be generated via Yarn and embedded in a .go file with go.rice beforehand.
Clone the repository and use the build make target to create a binary:
$ git clone git@github.com:dstotijn/hetty.git
$ cd hetty
$ make build
Docker
A Docker image is available on Docker Hub: dstotijn/hetty. For persistent storage of CA certificates and project databases, mount a volume:
$ mkdir -p $HOME/.hetty
$ docker run -v $HOME/.hetty:/root/.hetty -p 8080:8080 dstotijn/hetty
Usage
When Hetty is run, by default it listens on :8080 and is accessible via http://localhost:8080. Depending on incoming HTTP requests, it either acts as a MITM proxy, or it serves the API and web interface.
By default, project database files and CA certificates are stored in a .hetty directory under the user’s home directory ($HOME on Linux/macOS, %USERPROFILE% on Windows).
To start, ensure hetty (downloaded from a release, or manually built) is in your $PATH and run:
$ hetty
An overview of configuration flags:
$ hetty -h
Usage of ./hetty:
-addr string
TCP address to listen on, in the form "host:port" (default ":8080")
-adminPath string
File path to admin build
-cert string
CA certificate filepath. Creates a new CA certificate is file doesn't exist (default "~/.hetty/hetty_cert.pem")
-key string
CA private key filepath. Creates a new CA private key if file doesn't exist (default "~/.hetty/hetty_key.pem")
-projects string
Projects directory path (default "~/.hetty/projects")
You should see:
2020/11/01 14:47:10 [INFO] Running server on :8080 ...
Then, visit http://localhost:8080 to get started.
Certificate Setup and Installation
In order for Hetty to proxy requests going to HTTPS endpoints, a root CA certificate for Hetty will need to be set up. Furthermore, the CA certificate may need to be installed to the host for them to be trusted by your browser. The following steps will cover how you can generate your certificate, provide them to hetty, and how you can install them in your local CA store.
Generating CA certificates
You can generate a CA keypair two different ways. The first is bundled directly with Hetty, and simplifies the process immensely. The alternative is using OpenSSL to generate them, which provides more control over expiration time and cryptography used, but requires you install the OpenSSL tooling. The first is suggested for any beginners trying to get started.
Generating CA certificates with hetty
Hetty will generate the default key and certificate on its own if none are supplied or found in ~/.hetty/ when first running the CLI. To generate a default key and certificate with hetty, simply run the command with no arguments
hettyYou should now have a key and certificate located at ~/.hetty/hetty_key.pem and ~/.hetty/hetty_cert.pem respectively.
Generating CA certificates with OpenSSL
You can start off by generating a new key and CA certificate which will both expire after a month.
mkdir ~/.hetty
openssl req -newkey rsa:2048 -new -nodes -x509 -days 31 -keyout ~/.hetty/hetty_key.pem -out ~/.hetty/hetty_cert.pemThe default location which hetty will check for the key and CA certificate is under ~/.hetty/, at hetty_key.pem and hetty_cert.pem respectively. You can move them here and hetty will detect them automatically. Otherwise, you can specify the location of these as arguments to hetty.
hetty -key key.pem -cert cert.pem
Trusting the CA certificate
In order for your browser to allow traffic to the local Hetty proxy, you may need to install these certificates to your local CA store.
On Ubuntu, you can update your local CA store with the certificate by running the following commands:
sudo cp ~/.hetty/hetty_cert.pem /usr/local/share/ca-certificates/hetty.crt
sudo update-ca-certificatesOn Windows, you would add your certificate by using the Certificate Manager. You can launch that by running the command:
certmgr.mscOn macOS, you can add your certificate by using the Keychain Access program. This can be found under Application/Utilities/Keychain Access.app. After opening this, drag the certificate into the app. Next, open the certificate in the app, enter the Trust section, and under When using this certificate select Always Trust.
Note: Various Linux distributions may require other steps or commands for updating their certificate authority. See the documentation relevant to your distribution for more information on how to update the system to trust your self-signed certificate.
Vision and roadmap
- Fast core/engine, built with Go, with a minimal memory footprint.
- Easy to use admin interface, built with Next.js and Material UI.
- Headless management, via GraphQL API.
- Extensibility is top of mind. All modules are written as Go packages, to be used by Hetty, but also as libraries by other software.
- Pluggable architecture for MITM proxy, projects, scope. It should be possible. to build a plugin system in the (near) future.
- Based on feedback and real-world usage of pentesters and bug bounty hunters.
- Aim for a relatively small core feature set that the majority of security researchers need.
Support
Use issues for bug reports and feature requests, and discussions for questions and troubleshooting.
Community
Join the Hetty Discord server.
Contributing
Want to contribute? Great! Please check the Contribution Guidelines for details.
Acknowledgements
- Thanks to the Hacker101 community on Discord for all the encouragement and feedback.
- The font used in the logo and admin interface is JetBrains Mono.